by Felicien | Jun 19, 2019 | Education
Did you know you can use just about any Amazon Echo device to make phone calls for free? You can do the same in the Alexa app on iOS or Android, whether or not you have an Echo device. You can also call others in your contacts on their Echo devices instead of their phones. These services can be convenient, and they are real money savers for people paying per minute for their cell or landline phone. In today’s tech tip we’ll show you how to make calls with Amazon Alexa.
Step 1: Open the Alexa App on Your Phone
Making phone calls using Alexa is an opt-in service, meaning you’ll need to enable it and set it up before it will work. Open the Amazon Alexa app on your phone, and tap on the menu bars (likely in the upper left). Choose “Things to Try”. On that page, choose “Calling”. This area reveals several videos and explainers on how to get calling with Alexa set up.
Alternatively, you can simply ask your Echo device, “Alexa, how do I set up calling?” for verbal instructions. Those are nice, but you’ll end up needing to work in the app anyways. For that reason, we think it’s easiest to start in the app.
Step 2: Give Alexa Access to Your Contacts
In the Amazon Alexa app, open the Communicate tab by tapping on the Communicate button in the bottom row. If you’ve not done this before, the app will ask for access to your contacts. Tap OK to grant access.
If you want to use the Alexa app to make calls directly from your phone, you can do it from this screen. Simply select the contact you want to call, choose the right number (cell, work, or home), and the call should begin.
Step 3: Talk to Your Echo Device
If what you really want to do is make calls using your Echo device, you should be able to do so after following steps 1 and 2. You have to know the right lingo, however. You can start with a simple phrase like “Alexa, make a call.” Your Echo device will respond with a question of its own, asking who you want to talk to.
Some of your contacts can be reached multiple ways, so you’ll need to be specific with Alexa. Alexa should understand commands like “Call mom’s cell phone” or “call Shawna at work.” You can also call numbers not in your contacts list with “Alexa, call (555) 356-4321.”
To call another Echo device, simply say “Alexa, call Leslie’s Echo.” If Leslie has calling enabled on her echo, you’ll get patched right through.
If you want to explore phrases in more detail, look back at the “Things to Try” area in the app.
Note: Alexa Can’t Do Everything
One thing to note before diving into the world of phone calls with Alexa: Alexa and her associated devices do have some limitations. There are a few types of phone calls that Alexa can’t make. First, and most importantly, Alexa can’t call 911 or other emergency service numbers. These services need to know where you are, and even though you might think Alexa knows that, the functionality isn’t foolproof enough to support emergency calls.
Alexa also can’t (or won’t) call those pricey 1-900 numbers. (Yes, that’s still a thing.) Similarly, directory assistance and information lines of the 211, 411, or “star-88 on any cell phone” variety aren’t compatible with Alexa’s calling technology. For now, Alexa also won’t call internationally, nor will it respond to “call 1-800 CONTACTS” or other letter-to-number prompts.
Conclusion
Making phone calls through Amazon Alexa is a great way to save if you’re still counting minutes on your landline or cell phone plan. Follow the steps above to enable the feature and give it a try today.

by Felicien | Jun 19, 2019 | Education
An uptick of vendor consolidation in the Ambulatory electronic health records industry has been a cause for concern for many small and medium practices recently. The main cause for concern lies in the preparation and costs associated with integrating their patient health records into new programs that are made necessary with vendor acquisition, especially if the acquisition has forced a phase-out of their current EHR program.
According to KLAS Research, an Orem, Utah based IT Review Firm, EHR vendors have dropped from 1000 plus companies 10 years ago, to roughly 400 companies in total. Some of the larger companies responsible for merging and acquiring in the Ambulatory EHR market are Cerner, McKesson, Allscripts, Epic, and eClinicalWorks. Many see the opportunity for innovation, but these mergers have also created a unique set of challenges for small practices, Specialists and Outpatient Facilities. With these practices being reliant on the need to efficiently organize patient data as well as cross-share information to several labs, pharmacies, and other facilities in their networks, EHR has now become a necessary tool.
Market dynamics and technology advancements have proved that the move to electronic medical records systems is inevitable, but services once offered at low or no cost, now come with a monthly price tag. Service level changes, training costs, technology implementation, and practice continuity also serve as impact areas that Physicians should be prepared to address if migration to another system is required.
What About Technical Support?
Comprehensive Databases, such as Ambulatory EHR, will make technical support an important concern, not only for maintenance, but for any issues that may arise affecting day to day business. Will mergers cause reduced levels of tech support? Some physicians seem to think so. Practices reliant on specialized support options will now have to contend with an influx of other consumers operating on the same system, increasing help wait time and support availability. Frustration at rising costs, service level changes, and the elimination of special features in existing EHRs, have physicians worried that they will no longer be able to cater to their specific practice needs.
How to Prepare for Health IT Innovation
Ideally, Practices that are already utilizing EHR systems offered by the bigger players in the market have no cause for concern. For those practices that do find themselves needing to integrate into a new EHR system, preparation is key in order to avoid any potential negative impacts. The most important way to ensure a smooth transition is the current data organization. Physicians should understand where and how their data is organized, what format it is in, and the steps it would take to transfer it to another system. Current vendor communication and a review of contracts can also provide insight into costs and procedures of data migration, as well as a list of replacement vendors that would be best suited to practice needs if a switch needs to be made.
The Ambulatory EHR market will continue to make strides in innovation and technology advancement. Most of these changes are positive, like the introduction of Patient Portals, where data collection, tracking, and cross sharing have become streamlined and consumer friendly. Small Practices can avoid any potential negative impacts by simply understanding the data they collect, how to transfer it if they need to merge into another system, and by preparing a solid transition plan.

by Felicien | Jun 19, 2019 | Education
Cost-cutting measures are not unusual for organizations as they traverse the standard lifecycle of products and services. What you decide to cut during the lean times can have just as much impact as to where investments go when your business is flush with cash. Some organizations start their cuts in advertising and marketing but eventually make their way to technology projects. Managing expenses and balancing them with the associated risks is a critical task in organizations, but there are two places where the risk simply isn’t worth the savings in expense reductions: cybersecurity and proactive support for your business technology. Reducing your funds in these two vital areas could cause a negative impact on the organization that has a ripple effect felt for years to come. Here’s why these are the two places that you should never cut corners in your business.
Protecting Your Organization’s Business Systems and Data
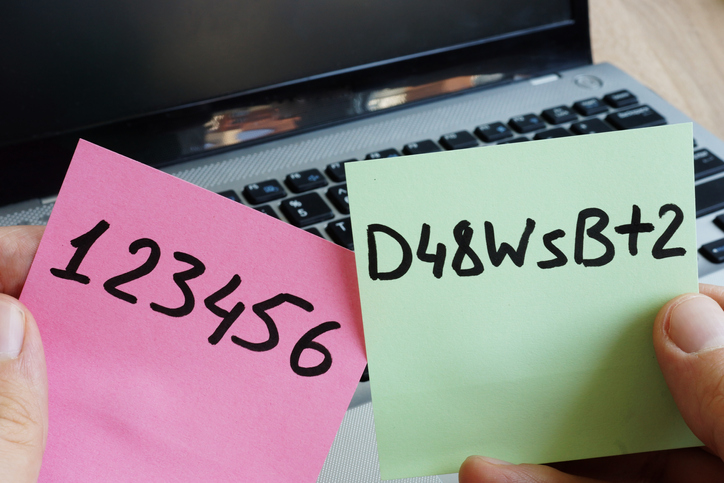
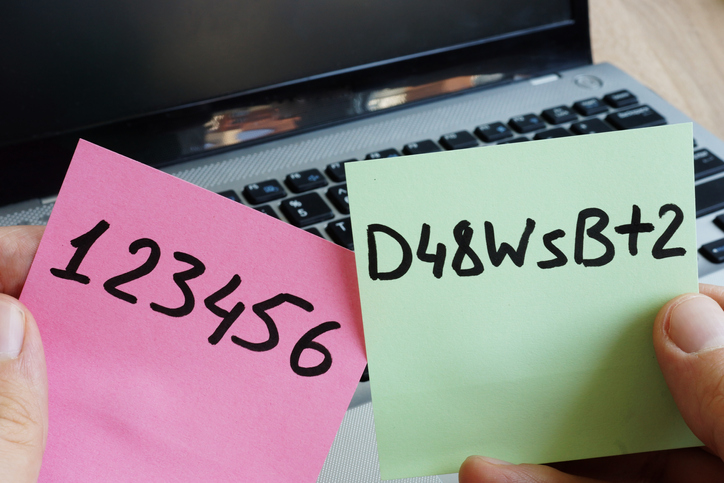
Cybersecurity is a broad term that refers to a range of activities including hardware protection, software patches, password requirements, staff training, server maintenance, cloud-based controls and more. There is no simple definition of what can be included in cybersecurity and business requirements change on a fairly regular basis. This alone makes it difficult to set a budget and stick with it — or reduce it over time. The ever-changing nature of threats that can effectively cripple an organization in a very short period of time means that your business will need to continually invest in learning and growth opportunities to reduce the risk to your organization.
Data protection is another facet of cybersecurity that demands consideration. From the 2018 GDPR (General Data Protection Regulation) to more recent requirements in various states, data privacy and compliance has come to the forefront of the security conversation. Businesses must first wrangle and then protect sensitive personal, health and financial data — not to mention securing their business systems from infiltration by hackers. Skimping on these critical tasks or attempting to do them in-house with limited resources can open your organization to significant fines if you’re found to be non-compliant with global or state-supported regulations.
Smoothing the Cost of Technology
It’s always tempting to cut out what could essentially be considered insurance: the ongoing maintenance and support of your technology hardware and software. When your business reverts to paying only for systems that are broken and unable to be used, you’re left with a hodgepodge of user complaints due to slowdowns that aren’t “bad enough” to be sent out for repair. Plus, you’re looking at a hefty fee for getting any break-fix work done quickly — and forget about being able to budget effectively by guessing what could potentially require repair or replacement during the year.
Proactive maintenance of your business systems allows business users to maintain a high level of productivity while also factoring your technology costs at a reasonable level throughout the year. It can be extremely challenging when you’ve exhausted your budget for break-fix support for the year, only to find that it’s only the beginning of the third quarter. In that case, you’re either siphoning funds from other crucial projects or trying to limp through the remainder of the year until you can reset your budget and resolve outstanding problems. Investing in proactive maintenance means you don’t have to question whether a fix is “important enough” to be resolved as long as the issue is within your service threshold.
Protecting your business from unnecessary risk can feel like a full-time job for busy technology leaders. Fortunately, IT managed services providers are able to help with both proactive maintenance and providing the high level of cybersecurity expertise that is needed to help protect your business from both current and emerging threats.
by Felicien | Jun 18, 2019 | Education
In early 2019, white-hat security expert Troy Hunt and other researchers shared a massive database of breached passwords and usernames. The stolen data constitutes 25 billion records and 845 gigabytes of stolen data.
While many of the collected records are from previously reported thefts, there are new records there, too. It’s a clear indication of regularity, scope and potential damage caused by poor password management.
That news coincided with Google’s announcement of its new Password Checkup extension for Chrome browsers. The extension is designed to alert and protect users who may have compromised credentials.
What is the Password Checkup Extension?
Password Checkup allows users to check if their Google account, and any other account you check into while using Chrome, has been potentially compromised during a previous data breach. Developed in partnership with Stanford University cryptographers, the extension is designed to give you critical information while safeguarding your data.
How Does Password Checkup Work?
After installing the extension, Google will alert users if they find potentially compromised passwords. The passwords are checked against a database of 4 billion known compromised credentials. Warnings are issued automatically, along with a recommendation to change the potentially compromised credential.
It’s important to note that the extension will not alert you to any outdated passwords or weak passwords. While those other factors can also lead to your account information being hacked, the Password Checkup only identifies known hacked passwords contained in databases.
What Does It Look Like When Password Checkup Is Activated?
The Password Checkup icon appears in your browser bar as a green security shield. The extension app will monitor your account whenever you use Chrome to log into a website or a service.
If it detects that the password is potentially compromised, a bright red warning box pops onto your screen. It features a warning sign and urges you to change your password. The box allows you to ignore the alert for the designated site. There’s also a link to learn more information via a page with more details about Password Checkup and how to change a potentially compromised password.
If for some reason you miss the red pop-up box, the browser extension icon turns from green to red.
Can Google See My Passwords if I use Password Checkup?
No. None of the passwords that the app uses are stored and personal information is not collected. The checked passwords are anonymized using hashes and encryption. Password Checkup was designed to prevent hackers from attacking it.
What Are the Risks of Compromised Passwords?
News stories are constantly reporting on the latest corporate data breach, revealing the thousands of records that were exposed and how that company is responding. The story behind the story is what happens to those stolen credentials.
In some cases, hackers sell information on the dark web. For users that do not know about the hack or aware but choose to do nothing, the consequences can be dire. Bad actors now can access accounts, make purchases, steal money or gain other personal information that can help to steal one’s identity.
People affected by stolen credentials can spend months or years resolving the issues related to compromised accounts. This work is time-consuming, costly and stressful.
Are There Other Tools to Check Compromised Credentials?
There are many other services that help monitor and detect stolen passwords, including websites such as Have I Been Pwned? and Watchtower and password managers like Dashlane and Keeper.
How Prevalent Are Data Breaches?
According to the 2019 Verizon Data Breach Investigations Report, stolen credentials are also an increasingly popular approach for hackers looking to gain access to cloud-based email servers. Stolen credentials are a particular issue for businesses in the accommodations and food services, financial and insurance, educational services, manufacturing and professional services industries.
What Can Be Done to Prevent Compromised Credentials?
For businesses, there are several steps that can mitigate the risks of data breaches that result in compromised credentials:
Develop and enforce rigorous password policies, including password complexity, reuse and expiration dates
Implement two-factor or multi-factor authentication that uses both known information, such as a stored password, and new information, such as a texted or emailed credential, (e.g. a one-time access code)
Centralized identity access management
Centrally managed single sign-on protocols
Google’s new extension is an excellent way to provide individual Chrome users with information that will protect themselves and their personal information. When combined with broader business rules, the extension should reduce the rate and severity of compromised credentials.

by Felicien | Jun 18, 2019 | Education
When you’re working hard to grow your business, you can get caught up in things that take your attention away from your technology. Before you know it, your IT system isn’t up to speed because you failed to update an operating system. We don’t want this to happen. This is why we’ve provided a checklist about Windows 7, its approaching End of Life (EOL), and what you should do.
It’s Time To Upgrade From Windows 7
Extended support for Windows 7 will end on January 14, 2020. This means that Microsoft won’t provide security updates for PCs running Windows 7. This could put your IT system at risk for security and reliability issues.
We recommend that you plan your upgrade now. And, if you run a business, we advise that you skip Windows 8 and upgrade to Windows 10 Pro.
Skip Windows 8 and Migrate To Windows 10 Pro
Windows 8 product enhancements (mainstream support) ended back on January 9, 2018. And reliability and security patches will end on January 10, 2023 (the end of extended support). This may seem like a long time from now, but if you’re upgrading anyway, shouldn’t you use the most current Windows program? Windows 10 Pro offers the very latest technology, and it’s built for business use.
Windows 10 Pro Will Benefit Your Business
Increased Security is incorporated with ongoing protections like Windows Defender Antivirus, BitLocker, a Firewall and more (at no extra cost to you).
Windows Remote Desktop ensures that you can access your files from any PC or tablet with an internet connection.
Automatic Cloud Storage will store and protect your Word, PowerPoint and Excel files from system crashes.
Sign In 3 Times Faster by using Windows Hello with Facial and Fingerprint Recognition.
Take Advantage of New Features In Windows 10 Pro
Windows Ink with Touch Screen & Digital Pen Capabilities
Windows 10 Pro pairs with Office Documents and Other Apps
Microsoft Edge with faster and safer web browsing, automatic form filling, type or write on webpage capabilities, and much more
Cortana voice-activated digital assistant integrates with your calendar and other Windows apps.
You Have Two Choices For Upgrading
1. Migrate your existing machines to Windows 10 Pro.
2. Replace your old computers with new Windows 10 devices.
Consider This Before You Migrate To Windows 10 Pro
Are your current apps compatible with Windows 10? (Check Microsoft’s App Directory to be sure.)
Do your existing computers meet these system requirements?
1GHz processor or faster
1GB RAM for 32-bit; 2GB for 64-bit
Up to 20GB available hard disk space
800 x 600 screen resolution or higher
DirectX 9 graphics processor with WDDM driver
There are 2 Migration Tool Options
1. Windows Easy Transfer
For a small number of computers or a single customized deployment.
Transfer files and settings via a network share, USB flash drive, or Easy Transfer cable.
Can’t use a regular USB cable to transfer files and settings
2. User State Migration Tool (USMT) 10.0
Best for large-scale automated deployments.
Uses .xml files to control which user.
Accounts, files, and settings are migrated.
Use for side-by-side migrations for hardware replacements, and wipe-and-load migrations.
Test The Quality & Performance of Your New System
Use the Windows Assessment and Deployment Kit (ABK) to test the quality and performance of your system, and to customize Windows images for large-scale deployments.
Need Help Upgrading To Windows 10 Pro?
We’re always here to help and answer your questions