by Felicien | Jul 9, 2020 | Education
Do you need to reset your computer system?
Resetting is different from simply refreshing or restoring a computer system. Resetting means reinstalling Windows but during the process, you delete your personal settings, apps (unless the apps originated with the computer), and files (unless you choose to keep them). Refreshing and restoring your computer doesn’t require deleting these things, the latter of which is a scary idea. You, however, will likely need or want to reset your computer system using Windows 10 if, for example, any of the below are present:
Your computer system often freezes, runs slow, or otherwise acts funny and trouble-shooting the cause will take hours or more.
You haven’t installed an app, driver, or an update recently, and the computer doesn’t work well.
You simply want to restart using a clean slate and don’t want to conduct a cumbersome old-fashioned install typical of Windows 8 and previous versions.
You want to resell, trade, or dispose of your computer or computer system.
Resetting your computer system using Windows 10 is a relatively short process that has been considerably refined since Windows 8. Resetting doesn’t require a product key or any other installation tools and amounts to a few basic steps.
Step-By-Step Process to Reset Windows 10
Before resetting your computer system using Windows 10, you want to make sure you have backed up your system. As a reminder, you will lose most––if not all––of your personal settings, files, apps, and drivers when you reset your computer. Once you decide that resetting is what you want to do, you have to decide which of the three basic methods is appropriate for you:
Reset using Settings. Use this option if you can access Settings from the menu.
Reset from the Sign-On Screen. Use this option if you cannot access Settings. It’s also the way to reset using what’s commonly referred to as the Safe Mode.
Reset from a Blank Screen. Use this option if the first two are not options.
Reset Using Settings
Select the Start buttonin the menu.
Select Settings> Update & Security> Recovery .
Click on Open Recovery settings.
From the Recover page and under Reset this PC, select Get started.
You then have three options from which to choose:
Keep my files > Change settings > Preinstalled apps On. This option reinstalls Windows 10 and allows you to keep personal files while removing settings, apps, and drivers you installed and restoring apps installed by the manufacturer. If you choose this option, you will be prompted on the Next screen on what personal files to keep.
Keep my files > Change settings > Preinstalled apps Off. This option reinstalls Windows 10 and allows you to keep your personal files while removing settings, drivers, or apps that either you or the manufacturer installed. If you choose this option, you will be prompted in the Next screen on what personal files to keep.
Remove everything. Under this option, you can either (1) leave Data erasure On, which is best if you will dispose of or sell your computer; or (w) leave Data erasure Off, which is less secure but also takes less time.
Before you actually start the resetting process, you will be provided with an outline of what happens when you reset your system. If you agree, then click the Restore button. The process can take up to an hour. You know it’s finished once a license agreement appears and you are asked to agree to it.
Reset Using the Sign-On Screen
Simultaneously press the Start button and the L key to render the sign-in screen.
Simultaneously press the Shift key and Power button.
While still holding down on the Shift key, click Restart, which appears in the lower-righthand corner. The computer will restart in Windows Recovery Environment (WinRE), which is also referred to as Safe Mode
A blue screen will appear giving you three options: (1) Continue; (2) Troubleshoot; and (3) Turn off your PC. Choose Troubleshoot.
From the Troubleshoot page, click on Reset this PC. The same Recovery page as mentioned above will appear. Choose Reset this PC.
The Reset this PC page will appear. Choose one of the three same above-listed options on the Reset this PC page and then follow the same process.
Reset from a Blank Screen
Confirm the computer is turned off.
Turn on the computer by pressing the power button.
As soon as it restarts, press the power button again to turn it off.
Repeat steps 1-3.
Restart the computer––it should start-up in the WinRE environment (Safe Mode).
You can now follow the same steps under Reset from the Sign-on Screen.
A Windows 10 Alternative to Resetting
Windows 10 also allows you to refresh your computer system by using the Give your PC a fresh start option. This option is useful when you want a fresh start but do not want all the factory software installed. This process takes a lot less time, like 20 minutes or so, and is preferable when you want to “reset” using Windows 10 because the computer isn’t working well and you recently installed a new app.
Whatever your reason is for wanting to reset your computer system, it’s good to know you have options when using Windows 10.

by Felicien | Jul 4, 2020 | Education
Microsoft Teams as an Alternative to Zoom
COVID- 19 induced lockdowns and social distancing measures helped spur Zoom’s growth. The video conferencing app managed to attract 300 million users by April 2020 compared to 10 million in December. Its rise to prominence left rivals like Facebook, Microsoft, Cisco, and Google scrambling for innovative ways to gain a competitive advantage.
However, privacy and security hiccups compromised Zoom’s popularity. Hackers infiltrated many meetings around the world in actions known as Zoom bombing. In South Africa, hackers beamed shocking images to parliamentarians during a virtual meeting.
The security and privacy concerns led to the banning of video conferencing platform by the NYC Department of Education. As a result, remote learning classes in New York switched to platforms like Microsoft Teams. Recent reports revealed that the Zoom app failed to encrypt messages end-to-end, which exposed user’s email addresses.
Microsoft Teams: The biggest threat to Zoom
Microsoft recently confirmed reports about a powerful new feature that is undoubtedly a game-changer in the videoconferencing sector. The platform can now handle up to 300 participants during a virtual video meeting. The technology giant introduces this feature when it has been launching a string of features in its push for the top spot.
The increased number of participants in a meeting is a boon for businesses and other organizations, which host large virtual meetings. With the Zoom app, virtual meetings can only accommodate a maximum of 100 participants. To increase the number of attendees, you need to use an add-on.
The gallery view in Teams enables users to view up to 49 participants during a virtual video call. Microsoft boosted the gallery view feature by adding 40 more people up from nine. The addition is a welcome move for multiple groups like exercise classes, business meetings, and schools.
Benefits of switching to Microsoft Teams
Many users are searching for a viable alternative to Zoom. Microsoft’s introduction of robust new features has enabled the Teams platform to stand out as a strong challenger for Zoom.
Many companies can find it easier to opt for Microsoft Teams because they are already using the tech giant’s other products. As the Teams app’s evolution gains momentum, some analysts from Credit Suisse predict that the platform is more likely to emerge as the greatest threat for Zoom in the long-term.
Experts also highlight Microsoft’s size and profile in the technology sector as its principal advantages. The Teams app also provides easy integration with the tech giant’s productivity suite. Microsoft can launch massive marketing campaigns, thus enabling it to reach potential customers at scale.
Privacy and security features in Teams
Microsoft Teams comes with a wide array of security and privacy controls designed to prevent vulnerabilities to hacking similar to Zoom bombing. These features allow you to monitor and control access to your company’s virtual meetings and sensitive information.
During the meetings, you can add, remove, and appoint both participants and presenters. Privacy controls empower you to regulate access to confidential material used in the presentation. Guest participants from outside your business gain limited access to sensitive details.
Moderation tools allow you to control how attendees post and share information. Microsoft Teams employs artificial intelligence to track conversations to prevent the transmission of inappropriate content or conduct. The app ensures data protection using advanced encryption methods. It complies with more than 90 regulatory guidelines, including FedRAMP, HIPAA, and GDPR.
Notable features in Teams
The platform comes with a sophisticated noise suppression feature to eliminate ambient noise from meetings automatically. Microsoft is planning to add a more advanced real-time noise-canceling feature that uses artificial intelligence. Additionally, Teams will introduce a raise hand feature to enhance convenience during virtual meetings.
by Felicien | Jun 28, 2020 | Education
How to Convert a User Mailbox to a Shared Mailbox in Microsoft 365
After converting your regular mailbox to a shared mailbox in Microsoft 365, you retain all your existing calendars and email. The only difference is that it will be visible to several people. You can convert your shared mailbox back to private in the future. It promotes teamwork and convenience.
Some of the most important things to know when converting from user mailbox to shared mailbox include:
The user mailbox you wish to convert must have a license -assigned to it before you can convert it to a shared mailbox. If it does not, you may not find the option to convert it. If you removed the license, add it back first. You can remove it back later.
Do not delete your old user’s account as you will need it to anchor your shared mailbox
With a shared mailbox, you can enjoy up to 500GB of data without a license. If you want more data, you must have a license assigned.
You can convert regular mailbox to shared mailbox by following these steps:
Find the Admin option after logging in to your Microsoft 365 account
Find the option ‘Active Users’ under the Admin option
Choose the user you wish to convert and click on the option ‘Mail Settings’
Click ‘Convert to shared mailbox.’
Click ‘Convert’ to finish the process
Using the Exchange Admin Center
Find the option ‘Exchange Admin Center
Click on the option ‘Recipients’ and then ‘Mailboxes.’
Find the user mailbox and select ‘Convert’ under ‘Convert to shared mailbox.’
If the mailbox is less than 50GB, remove the license from the user. Stop paying for it, but do not delete your user’s account. If you are converting it for a previous employee, check to ensure that they have no other way of logging in.
Converting the Mailbox of Deleted User
If you wish to convert the mailbox of a deleted user, follow these steps to complete the process:
Restore the deleted account
Ensure that it has an assigned Microsoft 365 license
Reset the password and wait for the mailbox to be created again
Convert it to a shared mailbox and remove the license from the user mailbox
Start adding members
Converting a Shared Mailbox to a Regular Mailbox
You can convert your shared mailbox back to a regular mailbox by following these steps:
Login to your account as admin and find the Microsoft 365 Admin Center
Click ‘Exchange’
Find the options ‘Recipients’ and then ‘Shared’
Click on the shared mailbox
Click ‘Convert’
Click ‘Convert to regular mailbox.’
You will receive a warning message asking for confirmation.
Click ‘Yes’
You must assign a license for the mailbox after conversion. You must also reset the password. The conversion can take a lot of time. When it is done, you will receive a completion message. Click ‘Close.’
After signing into Microsoft 365 again, you will find all the data from your shared mailbox.
In conclusion, Microsoft 365 is great for both regular and shared mailboxes. They all have unique features and benefits. A shared mailbox is an inbox type that allows you and other members of your team to send and receive emails from a similar address. It is a great option for companies that wish to promote teamwork. Since all members can respond to emails in the address, sharing work is easy.
If you wish to switch from user to shared mailbox, you can complete the process in a few simple steps. During the migration process, your data remains secure and integrated.
by Felicien | Jun 24, 2020 | Education
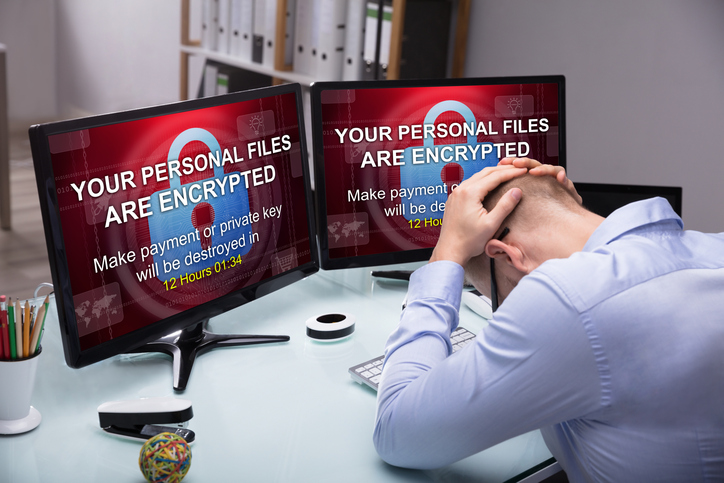
$150K Ransomware Payment
A recent news piece published by Tech Republic highlights the discouraging reasons why too many businesses fall prey to hackers and pay ransoms for their digital property. Perhaps nothing adds insult to injury quite like someone burglarizing your organization and then making you pay for their crime.
A recent $150,000 ransom paid in Bitcoin to regain control of one small business’s digital assets reveals why so many cybercrimes go unreported. As staggering as the data breach statistics are, they may just be the tip of the spear. Security journalist Karen Roby conducted a Q&A with an unidentified CFO who made the decision to set aside pride and succumb to a hacker’s demands.
“His company chose not to get authorities involved given the value that was at stake, and the company’s immediate need to gain back control of its network,” Roby reportedly stated. “We’re hoping his first-hand account will help you better understand what these types of ransomware attacks look like and give you an idea of how to better protect your own organization.”
How Do Ransomware Attacks Happen?
Ransomware attacks rank among the more prevalent methods used by digital thieves. The underlying strategy mirrors that of taking someone hostage and demanding payment from loved ones for their safe return.
In these cases, a company’s digital assets are taken hostage by inserting malicious software that effectively gives hackers total control of a network. Email remains the most-used delivery system. When someone in an organization gets tricked into clicking on a link or downloading a file, the ransomware application enters the network and hackers take control of the system and devices.
In order to regain control, cyber-thieves demand payment — typically in Bitcoin — in exchange for a decryption code. Like real-life hostage-taking, paying ransoms does not necessarily ensure the criminals will hold up their end of the bargain. Sometimes ransom-payers never receive the code. Other times, hackers delete systems to wipe away any digital fingerprints.
Why Some Decision-Makers Pay Ransoms
A ZDNet article called “Ransomware attacks: Why and when it makes sense to pay the ransom,” highlights why more businesses pony up rather than contacting the authorities. Written by Larry Dignan, the piece points out that the decision often comes down to cold financial calculations.
“Now paying ransomware is likely to go against conventional wisdom. The practice may also make you throw up in your mouth,” Dignan reportedly states. “However, there are real costs to having your company or city dead in the water for days. Paying ransomware should be viewed as any other business decision.”
In the case of the Tech Republic Q&A, the small business promptly contacted a third-party IT professional to assess the potential fallout of not paying the hacker’s demand. A quick review of the outfit’s digital assets revealed that the cybercriminal did not necessarily have control of what many consider to be the most valuable data. These typically include the following.
Banking information
Healthcare records
Personal identity information such as Social Security numbers
Intellectual property files
“The third party that we spoke to that were acting as our agent between us and the hackers. They said, ‘This is strange. You don’t really have anything they can hold over your head other than just stopping your business.’ But we engaged them quickly,” the ransomware victim reportedly said. “Ironically, they worked straight through on a Sunday to help us and by Monday morning we were in full agreement, and they began the conversation with the hacker group to see what we could get done.”
The third-party negotiated the ransom of $400,000 down to $150,000 in what took on the appearance of a corporate contract negotiation. The process revealed that some hackers conduct themselves like ordinary businesspeople. An encryption code was delivered, luckily, and this criminal outfit even offered tech support to the victimized company if they ran into problems getting computers back online.
“Yeah. I mean, if anything has made me laugh about this whole situation is that it’s just the selective morality of, ‘Hey, we know we’ve robbed you of money and your files and held you at our whim, but by the way, we’re here to help 1-800 …’ It’s unbelievable,” the victim reportedly said.
The Tech Republic’s microcosm looks at why organizations pay ransomware demands points out that some are overly reliant on their network. Failure to have a go-to backup system or secure digital assets that can be leveraged leaves industry leaders with a hard choice. Either pay up or sustain even greater financial losses. Bitcoin payouts are the hidden cost of subpar cybersecurity.
by Felicien | Jun 18, 2020 | Education
The Best Way to Switch IT Managed Service Providers
The COVID-19 lockdowns have naturally changed how many organizations and companies operate. Educational institutions are embracing virtual classes, events that were previously held in person are now fully virtual, and a whopping 98% of employees worked from home to avoid spreading the novel coronavirus. Sadly, not all IT managed service providers were able to keep up with their customers’ needs during this challenging time, leading disaffected business owners to search for new IT managed services that can handle a company’s current and future IT challenges.
While finding a competent IT service is imperative, it’s also vital to know how to change companies without disrupting your current IT operations. The following are some expert tips that can help a company transition to a new IT service safely and smoothly.
Switch First
Don’t tear up your contract with your current IT managed service provider until you find another provider that can take their place. Furthermore, you’ll need your new provider to get to work on your IT set-up right away. Once your new IT service has everything under control, you can pull the plug on your former IT service.
What does this operation entail? Here are some steps you’ll need to take to make sure your business is ready to switch IT managed services:
Make sure you have all your login information and administrative access to all your accounts. Any decent IT managed service will provide you with this information even before you ask for it. Sadly, some subpar services try to hold onto your information to force you to continue to work with them.
Have your new company do a thorough cybersecurity assessment of your business to ensure there are no back doors that former IT technicians can use to gain access to your valuable company information.
Let your staff members know that you will be changing IT managed services by a specific date. Inform them of new protocols that will be put in place once you make the switch.
Schedule IT training sessions with your new managed IT service as soon as possible so your staff members can learn how to master new programs and cybersecurity rules quickly and easily.
What Does a Good Managed IT Service Look Like?
Selecting the right IT managed service provider to replace your current IT service is no easy task. Here are some tips that can help you make smart decisions.
Make sure the IT managed service is familiar with your industry.
Look up reviews online and ask prospective IT managed services to provide references from clients they have worked with in the past.
Ask about the pay structure. It should be a fixed monthly price, with allowance to scale services as the need arises.
Make sure the IT service can meet not only your current but also future needs.
Choose an IT service provider that puts a premium on cybersecurity services. Data breaches are becoming more commonplace than ever, with more than eight billion records exposed in the first quarter of 2020 alone.
Switching IT managed services can be challenging. It shouldn’t be done in a hurry; at the same time, you shouldn’t hesitate to find a new service provider if your current one is unable to meet your present and future needs. Do careful research to ensure your new provider is the best fit for your business and then start the transition process before notifying your current IT company that you will no longer use its services. Doing so will protect your business from disruptions while improving your IT efficiency and security.

by Felicien | Jun 15, 2020 | Education
Have You Tried The Microsoft Edge Browser?
Microsoft’s Internet Explorer has been around from the early beginnings of the World-Wide Web. Over the years, it was sometimes immersed in controversy since it was “built into” some previous Windows versions. Well, not quite, since knowledgeable users knew how to install other browsers. But when Windows 10 came along, along with it came a new browser, Microsoft Edge. Below are some interesting, frequently asked questions.
What Great Things Can Microsoft Edge Do?
The following wonderful features exist on the newest Chromium-based version of Microsoft Edge, released January 15, 2020.
It has a new Collections feature that helps organize favorite webpages.
Web Note allows you to annotate web pages you find with a pen, highlighter, or typed notes. You can even do artful doodling on those pages, then save them in Edge or into MS OneNote.
It natively supports 4K video viewing, Dolby Audio, and Dolby Vision.
It runs on and syncs passwords, favorite websites, and settings on macOS, iOS, and Android. A Linux version is also rumored to be in the works for release later in 2020.
We are all familiar with horizontal web page tabs, but Edge also has an option to make them vertical, which is great for having lots of tabs open at the same time.
When you use passwords, Password Monitor will check autofill passwords against a database to see if they are in use elsewhere.
As with all great browsers, Edge also has a Privacy Mode.
Does Microsoft Edge Have Good Internet Protection?
The World-Wide Web, the wild-wild-West of the Internet, danger lurks all around. Cyber-thieves could use adware, malvertising, pharming, formjacking attacks, and man-in-the-middle browser attacks. Webpages may have malicious or poorly programmed scripts able to harm your computer and compromise your security. MS Edge is one of the major browsers in use, so all the reputable security software companies work together with Microsoft to create safe, seamless browsing experiences. Microsoft is continually being attacked from all sides, so its products are always being updated whenever issues are discovered.
Even if you were to accidentally lose or turn off your computer protection software suite of products, MS Edge works with other Windows applications to protect against the most common Internet hazards.
How Often Is Edge Updated?
Windows 10 users know that Microsoft has monthly updates for their systems. MS Edge will sometimes be updated at the same time. The user can also manually do updates or turn on automatic updating.
Is Microsoft Edge Based on Chromium?
The first version of Microsoft Edge came with the launch of Windows 10 using a proprietary Microsoft technology. Starting on January 15, 2020, Microsoft launched a new Google-Chromium-based Edge browser. In some ways, Microsoft’s version is more advanced than Google’s Chrome. For example, it already has anti-tracking defenses built-in. Edge has its own add-on market, however, add-ons can also be obtained from the Chrome Web Store.
Do I Have To Use Microsoft Edge?
If you use Internet Explorer 11 or an earlier version, you are probably using an operating system that will eventually no longer be supported. When that operating system reaches the end of its lifecycle, Microsoft will also phase out all support for that version of Internet Explorer.
However, you can use Google Chrome, Mozilla Firefox, and many other browsers. Each browser has its strengths and weaknesses. Hard-core users of Chrome often find that MS Edge will often work where Chrome fails.
Should I Use Microsoft Edge?
Does your company require you to log in from home to get access to special web-based database applications? If so, you want to first check with your corporate IT office to see if their software is running software using legacy DLLs: ActiveX Controls, Silverlight, or Java. It is very expensive to make reliable, stable custom controls for specific company needs, so your IT department may want you to wait before trying to access their website for home-based work purposes. However, they may also give you special instructions on how to configure Microsoft Edge to run in IE mode or enterprise mode. Remember, for home-based work with established companies, ask them what upgrades work best before trying something new.
What About Edge with Adobe Flash, ActiveX, Silverlight, or Javascript?
Adobe is ending Adobe Flash after 2020, but Edge supports web pages with and without it. Edge does not support BHOs like Silverlight or Java, nor ActiveX controls. For operating systems that still support Internet Explorer 11, Edge can be set to open web pages with those technologies in IE 11 automatically.
Should I Try the New Microsoft Edge?
Yes! But make sure you first learn it on a personal computer or device. Anybody who does research on the Internet will like the new features within the Edge Browser.