by Felicien | Oct 1, 2018 | Education
There’s a new Gift Card scam going around that has already cost consumers lots of money, frustration, and headaches. Here’s how it works.
You’ll get an email from a friend or relative asking you to go buy them a gift card. The email will say that your friend or relative has been busy or sick and unable to get to the store. Once you get the card for them, they’ll ask you to take a quick photo of the gift card code on the back and send it to them. Once you do this, they can cash out the gift card and you lose your money. It happens just that quickly.
Can You Help Out a Friend?
This scam has been working well for several reasons. Usually, the email comes from someone you know, maybe a sibling, parent, or aunt. Of course, you want to help them out, right? But one thing many consumers don’t realize is just how simple it is to hijack an email account. This is easy work for any hacker worth his salt.
For some reason, people just believe that the email is legit and never take that extra step of calling their friend or relative and just asking them, “Hey, did you send me an email about buying you a gift card?” That’s all it would take to avoid being a victim here.
Instead, most people will run down to Walmart or Target, buy the gift card, take the photo of the code on the back and think they’re doing a great favor for someone.
After you send the pic of the code back to the hacker, they will move very quickly to cash out the gift card and you’ll lose all your money. Later, of course, you’ll learn that your friend did not make such a request and now you feel silly for not double checking. After all, we should we savvier than that as consumers, right?
New Apps Make Scamming Much Easier
Unfortunately, these types of scams have been working well for many years. Plus, new apps like Raise make it easy to turn unused gift card balances into money.
Though victims do sometimes reach out to local police for help, this is actually not a crime. I know that most people are stunned by that news, but it’s true. Because you were a willing participant and you initiated the action with intent, no fraud was committed. So now you’re out the cost of the gift card and there’s really nothing you can do about it.
Just In Time For the Holidays
Authorities are warning consumers that this scam will be prolific all throughout the holidays. That’s why it’s so important to spread the word. Let your friends and family know that if they get a request like this from you or anyone, be sure to stop and call the person. Ask them if they really sent the email asking for a gift card. It only takes a couple of minutes to do this and it can save you $50 or $100 bucks.
Other Scams to Watch Out for During the Holidays
Hackers infamously took over the Rio Summer Olympics a few years back using social engineering to exploit the event. Though some were shocked, social engineering has been around awhile and is used every day to trick business owners. This scam costs Americans millions of dollars each year and hackers find new ways to make their tricks even more effective.
Phishing Scams
Used more frequently than any other, phishing scams have become so widespread that it’s difficult to get accurate results of the losses incurred.
PhishMe is reporting that these scams are growing by at least 65% per year.
Kaspersky Labs claims that during the first quarter of 2018, its anti-phishing system prevented more than 107 million attempts to connect users to malicious websites.
A Barkly reports shows that 85% of companies have fallen victim to this scheme.
How It Works
Phishing scams work relatively easily. It’s not rocket science, as they say. You get a legitimate sounding email that seems to be from your bank or credit card company. These emails often use fear and urgency to make victims take action before double checking the legitimacy of the email.
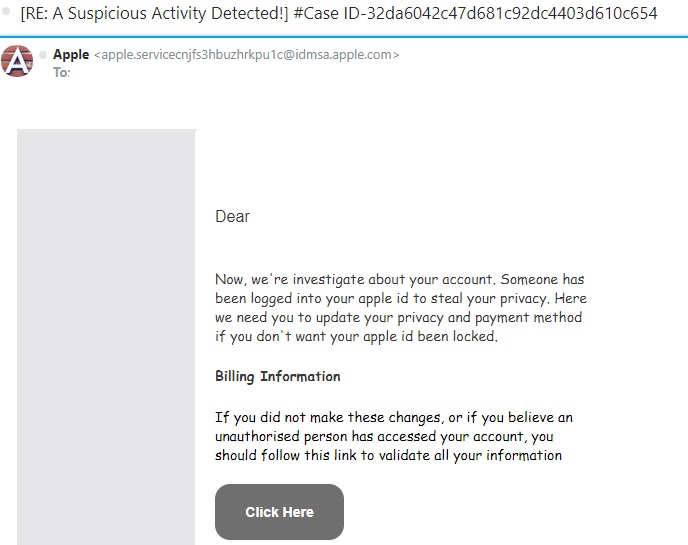
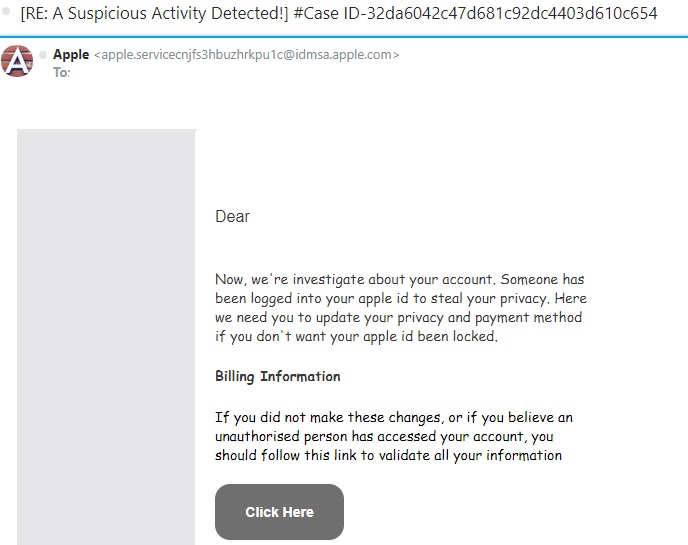
Below is an example. This scammer claims to be contacting you from Apple. If you check out the “From” address, you can quickly see that it’s not a legitimate Apple email account.
Another big clue is that words are misspelled and the grammar is very poor. You can tell that this email was written by someone (probably from Eastern Europe) who has very bad English skills.
NEVER click the link in a suspicious email like this one. Once you do, the cyber thieves can download malware or ransomware to your computer. They may also redirect you to a site where they steal your banking and credit card information. At the very least, they will steal your log-in information for your Apple account and then hijack it.
Final Tips
In order for consumers to avoid being a victim during the holidays, it’s important to watch out for these types of fraudulent activities. Never click a link in a suspicious email. Instead, open a new browser page and navigate to the website the way you ordinarily would. If there’s something wrong with your Apple account, a bank account or a credit card account, you’ll have a letter in your Inbox explaining what happened and what you need to do.
By using a little common sense and double checking when something feels suspicious to you, we can all avoid being victims this holiday season.

by Felicien | Oct 1, 2018 | Education
The Internet Crime Complaint Center (IC3) released a public service announcement at the end of September 2018, alerting companies about the risks of allowing RDP endpoints to be exposed online. The IC3, a division of The US Federal Bureau of Investigations (FBI), is sending out the alarm to U.S. businesses about their concerns that millions of RDP endpoints are visible online and susceptible to manipulation.
What is RDP?
RDP (Remote Desktop Protocol) is a Microsoft registered technology created in the 90s that permits a user to log into a remote computer and interact with its OS through a visual interface that gives the remote user access to its mouse and keyboard input. The remote desktop was designed for a computer technician to be able to help a customer who had limited or remote access.
RDP access is hardly ever enabled on home computers, but sometimes it is turned on for workplaces in enterprise networks or for computers situated in distant locations. RDP conveniently allows system administrators to access the computer, without physically having the computer in front of them.
Why is IC3 Concerned?
In its September press release, the FBI states that the number of computers with an RDP connection left open on the Internet has gone up dramatically since 2016. IC3 is observing numbers and trends by cyber-security firms in the past few years that are alarming.
ZDNet reported that Rapid7, a multi-product analytics and automation company, has seen nine million devices with port 3389 (RDP) opened on the Internet in early 2016, and then suddenly rose to over 11 million by the end of 2017.
Also, IC3 is seeing a steady stream of incident reports where hackers have acquired initial traction into victims’ networks through the computers with an open RDP connection.
The Rise of Ransomware Attacks
Over the past three years, a cluster of ransomware families were particularly designed to access a network by hackers who jumped in through an open RDP server.
Ransomware particularly designed to be infiltrated via RDP involves strains such as LockCrypt, Horsuke, CryptON, SynAck, Scarabey, Bit Paymer, Xpan, RSAUtil , Crysis, Samas (SamSam), Globe, DMA Locker, Apocalypse, LowLevel, Bucbi, Aura/BandarChor, Smrss32 and ACCDFISA.
How Do Companies Secure Themselves Before It’s Too Late?
IC3 has collaborated with the Department of Homeland Security (DHS) and published a report for companies to use to ensure RDP security.
Six Ways to Improve the Security of Network Infrastructure Devices
The National Cybersecurity and Communications Integration Center (NCCIC) has published six security measures for companies to ensure safety for their network.
Segment and Segregate Networks and Functions
Security engineers should study the overall layout of their framework, which includes both segregation and segmentation. A successful security tool for accurate network segmentation is to stop a hacker from spreading abuses or the ability to laterally move through an internal network. If the network is inadequately segmented, intruders can easily spread their control of analytical devices as well as obtain entrance into sensitive data. A securely segregated network can restrict malicious incidences and reduce the effect that intruders can have if they gain a foothold inside the network.
Limit Unnecessary Lateral Communications
Permitting unprotected communications between colleagues involving a workstation-to-workstation situation sets up grave weaknesses. This can permit a network hacker easy access to spread their attack to multiple systems. Once penetrated, the attacker can create backdoor manipulation throughout the network. When a hacker has backdoor access, they have an easier time of maintaining their presence inside the network and keeping users from removing the intruder.
Harden Network Devices
A basic way to boost a company’s network infrastructure security is to protect networking devices with secure designs. The best practice for a company is to implement the recommendations that government agencies, organizations, and vendors resource. Their guidance allows a business to be safe and stay within site security policies, and industry practices.
Secure Access to Infrastructure Devices
A company can give administrative freedom to allow specific users access to data and resources that are not broadly obtainable by the general public or all employees. Limiting these administrative privileges for infrastructure tools is vital for security because hackers will infiltrate administrative privileges that are inadequately approved.
Ways to secure access for infrastructure devices include having a multi-factor authentication process to confirm a user’s identity and closely monitor and manage the user’s access.
Perform Out-of-Band Management
Out-of-Band (OoB) management incorporates different contact paths that remotely manage your network infrastructure devices. These devoted communication paths can differ in configuration to involve areas such as physical separation and virtual tunneling. In applying for OoB access, it will strengthen your security by restricting access and dividing user traffic from the network management traffic.
Validate The Integrity of Hardware and Software
Products purchased and downloaded through unauthorized channels are more than likely a reproduction or inferior in their use. Several media outlets have reported the use of grey market hardware and software in the workplace. Unlawful hardware and software cause the users’ information to be at risk. Because they have not been carefully tested to meet superior standards, grey market products can present risks to the network. These risks can lead to breaches in the supply chain and allow opportunities for malicious software and hardware to be installed unbeknownst to the user. Compromised hardware and software can affect the network and give away the confidential and valuable information. Companies should regularly check the integrity of software.

by Felicien | Oct 1, 2018 | Education
As technology continues to become more widely used in the legal sector, it is apparent that even the most traditional offices should adapt. Technological advances, however, are occurring quickly. Not all attorneys and legal support staff are equally prepared to manage these new systems themselves. They do not, necessarily, require an entire IT department. This is where the right managed services provider (MSP) can be instrumental.
Managed service providers are companies that manage their clients’ IT infrastructure remotely. These are generally set up as a subscription per-device, per-user, or all-inclusive plan. Since providers have access to sensitive information, it is vital that the decision regarding which to choose is made carefully. Consider the following before searching for the right provider.
Why Would a Law Office Benefit from Having a Managed Services Provider?
Outsourcing IT management would reduce the stress and effort of maintaining the devices and network required to run a law office. Along with streamlining the day to day operations, a managed service provider will increase efficiency. For example, it would provide the following:
Adaptability to technological innovations
Access to advice, knowledge, and skills
Better business continuity and service
Better operations
Improved regulatory compliance
Increased efficiency
Increased IT security infrastructure
Reduced costly, technology-related risks
Streamlined operations
Although initially, it will add to the operating expenses, with the increase in efficiency it will reduce expenses over time.
Why Should Law Offices Choose an MSP with Industry Experience?
As with any service or product, the number of years it has existed indicates how well it can be expected to perform. Therefore, a more experienced provider is likely to have been tried and tested. Mistakes have already been made and solutions discovered. They have become seasoned professionals. Seeking a managed services company that has been around for a while reduces the chances that they are still figuring things out.
Be choosy. A qualified managed services provider may be capable of handling a new business with expertise. An industry-specific provider will handle it better. The legal profession is a highly-specialized vocation. It has a precise nomenclature and failure to use the correct word or phrase could result in big trouble.
An IT with legal experience is better suited to managing the services of a law office than an IT with a more general history. Choosing a provider with legal experience ensures they are able to anticipate potential issues, as well as understand the practice’s operational needs.
Why Should You Select a Provider with an In-House Network Operations Center?
Many managed service providers decrease the cost of their overhead by outsourcing their Network Operations Center (NOC). Although this may be fine for many companies, it could present problems for a heavily-regulated business like a law office. With the strict regulatory mandates, it is necessary to ensure that not only does the service provider adhere to them, but that their third-party NOC does, as well.
What Is Meant by Quality of Service When Comparing Managed Service Providers?
Determine whether potential providers outsource or handle service aspects in-house. If they handle in-house, inquire into their staffing levels. Do they have established procedures for various tasks? Do they have enough personnel to troubleshoot problems for clients?
A high-quality managed services company should also be able to have reasonable response times. They should offer accurate estimates for how long it takes for them to fix various problems that may arise in the future.
What Is the Importance of Innovation and Scalability?
Choosing a provider that adopts the most recent technology and offers the newest services ensures the office remains contemporary. An innovative IT managed services provider is able to use the latest strategies to address daily operations, as well as any potential problems that arise. This provides an edge over other, less modern law practices.
Additionally, when comparing MSPs, it is a good idea to address scalability. Like any company, a law practice is liable to grow and change. The right service provider should be able to accommodate this expansion. They should have enough experience that they can answer how they would handle these issues based on how they have in the past.
In Conclusion
Whether it’s a new practice or a well-established partnership, most law offices could benefit from hiring a managed service provider for their Information Technology. By following these suggestions, savvy lawyers can select the right provider for their needs. Along with the many other perks, it helps ensure attorneys and office support staff have more time to focus on other, more important aspects of their jobs.

by Felicien | Sep 28, 2018 | Education
Facebook Was Breached
Were You Or A Facebook Friend Affected?
Facebook has confirmed that more than 50 million user accounts have been breached. They made the announcement today, Friday, September 28th. However, their engineering team discovered the security breach back on Tuesday, September 25th, 2018. They tell us that the vulnerability has been fixed and the breach was reported to the appropriate authorities.
How Did This Happen?
Hackers stole users’ access tokens through Facebook’s “view as.” This is a feature that lets you view what your profile looks like to other Facebook users. The flaw in this feature allowed hackers to take over 50 million user accounts.
If you’re like me, you may have received notices from some of your Facebook friends this week that someone took control of their accounts. Perhaps they were affected by this breach.
What Are Access Tokens?
These are the digital keys that keep us logged in so we don’t need to re-enter our password every time we use Facebook. With this information, hackers can take over our account.
Here’s how Facebook explains what happened:
“Attackers exploited a vulnerability in Facebook’s code that impacted ‘View As,’ a feature that lets people see what their own profile looks like to someone else. This allowed them to steal Facebook access tokens which they could then use to take over people’s accounts.”
What Now?
Facebook reset the tokens of all those affected. They also logged off 40 million additional users as a precaution. If you are one of these people, you’ll need to log back in the next time you use Facebook.
According to Facebook, their investigators are in the early stages of their investigation. They are temporarily turning off the “View As” feature while they conduct a thorough security review
What Should You Do?
If you have trouble logging back into Facebook, or you forgot your password, visit Facebook’s Help Center.
If you’re like me, you take extra precautions when you hear about breaches like this. If you want, you can visit the “Security and Login” section in Facebook settings. It lists the places where you’re logged into Facebook with a one-click option. If you choose, you can log out of them all.

by Felicien | Sep 28, 2018 | Education
The September update of Office 365 includes some major additions and changes to tools such as Microsoft Teams, PowerPoint, and Excel, just to name a few. It is important to keep up with these developments, so here is a list of the major advancements of which you need to be aware.
Microsoft Teams: Skype, Selective Do Not Disturb, Wiki App
Many users have been looking forward to the day when Skype is integrated into Microsoft Teams, and that day has finally come. You can now use Microsoft Teams for cloud-based meetings that can have up to 250 participants, powerful messaging features, and some awesome calling features.
One of the most practical additions to Microsoft Teams is to set up a selective Do Not Disturb status so that some people can still feel free to reach you (e.g., your supervisor or manager).
It’s simple to setup: Click on your avatar, Settings, Privacy, and then select the individuals who you still want to receive notifications from.
Another one of the new updates in Microsoft Teams is the Wiki app, which can be accessed through the left-hand navigation panel using the More Apps ellipsis. This app allows you to see the wiki pages you are a part of, keep track of your own private notes, and see the notes you’ve most recently been editing.
PowerPoint: Embedded Fonts
Have you ever prepared a presentation on one computer and had it looking just perfect, only to open it up on another computer and the fonts looked totally different? There is a way to keep this from happening: embedding the fonts in the PowerPoint deck when you save it.
Go to Save As > Browse > and then go to the Tools drop-down box in the bottom corner of the dialog box. In the Tools drop-down, click on Save options. Toward the bottom of the box that pops up, you will see an option to “Embed fonts in the file.” Check that box, then click OK and save as you normally would.
This option used to be only available on Windows devices, but the new update of Office 365 also makes it available on Office for Mac for Office Insiders. To access it on a Mac, go to the PowerPoint menu and click on Preferences, then Save. The Font Embedding option will be in the dialog box that appears.
Excel: Flow Integration
Microsoft Flow has been integrated with Excel, and is accessible via an Excel add-in. This will allow you to connect your data to services like Microsoft Teams, Twitter, SharePoint, Dynamics 365, Office 365, and more. You will be able to create and trigger on-demand flows for selected rows in spreadsheets that are hosted on OneDrive for Business or in SharePoint.
With this integration that uses the ‘For a selected row trigger’ and the Flow launch panel, you can create and trigger on-demand flows for selected rows in any Excel table on spreadsheets hosted in SharePoint or OneDrive for Business.
Access: Improved Visualization Tools
Users have been requesting more visualization tools for their data contained in Access, and that is exactly what Microsoft has provided. Not only have charts been made easier and more intuitive to create, but additional chart types have also been added. For power users who developed their own Active-X solutions to the challenge of creating charts for forms and reports, their solutions will continue to work.
Power BI: Export to PDF
This is another update that came about as a result of user feedback: the ability to export Power BI reports in PDF format where they can be shared with others. This will only be available in the desktop version of Power BI for right now.
Microsoft has also added an “Ask A Question” to the Power BI Desktop which will be globally available in the client. What this means is that you can use natural language queries to explore your data and allow report users to ask their own questions.
SharePoint: More Granular Control for IT Admins
In previous releases, if a group of users was not allowed to create Office 365 groups, they would be limited to creating Classic SharePoint sites. They could not create modern SharePoint sites. The new release has changed this: the IT administrator determines who can create classic SharePoint sites, who can create modern SharePoint sites, and who can create Office 365 groups.
Security
Microsoft Cloud App Security is a powerful tool that evaluates every app used in terms of industry-specific standards, compliance, and regulatory certifications. The goal of this is to make sure that your company can make informed decisions on the type of apps that are most appropriate for not only your needs, but your security. This new release also checks for GDPR compliance and can generate a C-level report on critical findings.
Conclusion
While this isn’t an exhaustive list of all the new features and changes available in the September update of Office 365, it does present the ones that are going to have the greatest impact. However, it’s always a good idea to be cognizant of new developments even if they don’t directly impact your daily work.