by Felicien | Jan 7, 2019 | Education
How Much is Spent Worldwide on IT Costs?
Worldwide IT costs in 2018 hit an estimated $3.7 trillion, up 4.3 percent over the prior year, according to the Gartner, Inc. With so much at stake, it’s essential for all companies that utilize IT to consider the pros and cons of a traditional IT approach versus moving more and more functionality to the cloud. Finance considerations are one of the top considerations, but control over assets and data security are also vitally important. Therefore, it’s essential that the CIO is prepared to talk about the differences in language other executives can understand.
Why It’s Difficult to Explain Cloud Costs to the C-Suite?
CIOs sometimes have a hard time explaining the difference between cloud services (typically a SaaS with monthly operating expenses) and traditional healthcare IT models that may involve paying cash for software and equipment to own them outright (a capital expenditure). This comparison needs to factor in the monthly cost to run on-premise data centers, as well as the allocation of capital expenditures, such as hardware, licensing, etc. Non-financial factors include company policies that favor ownership versus rental models for IT hardware and software. Unless the cloud expense is much higher, the C-suite should lean toward cloud economics as a more strategic approach. It governance policies may also need to be revisited to support cloud computing trends.
Moving from a Cost Center to Strategic Partnership Model?
Healthcare organizations deliver healthcare services but are also digital companies. Cloud computing is now a critical component that brings the latest technology to the table, perhaps improving outcomes. It’s essential to help the C-suite understand this. One analogy that works is comparing it to another service based on consumption. Just as the utility or electric bill varies based on actual consumption, cloud computing cost varies based on changing usage. Building an accurate forecast prepares the leadership team for the hit to OpEx and the P&L. It may still be a tough sell, and the IT team might need some finance talent to track and adjust usage trends to keep the cloud cost forecast up-to-date.
How Can a Flexible OpEx Model Help Healthcare IT?
If a healthcare company needs to change directions fast to incorporate new diagnostic tools, therapies or IT innovations, an OpEx model is the fastest way to respond. Many times, the CIO is seen as someone holding fast to a traditional CapEx model or as someone rushing change before the organization is ready. Instead of letting the decision point be a source of contention, a mix of CapEx and OpEx could be the best answer. In this hybrid model, the decision to use a cloud-based approach versus a traditional on-premise solution would hinge on individual decisions about risk management and financial requirements, resulting in a variety of local and managed private cloud services as well as public cloud services.
What are Some Convincing Tactics for other Executives?
The difference boils down to buying software and hardware at once or paying a subscription. To show healthcare executives the advantages of the cloud, CIOs must demonstrate the benefits of the OpEx (or hybrid) model in a quantifiable way. For example, consider the CapEx model for buying a piece of hardware. The hardware has to be secured and configured, and the terms and conditions must be approved by the legal team before software can be installed. You put out a lot of hard-earned cash and wait months to actually use the product. The process takes months and ties up precious resources. In the cloud model, new solutions are available quickly without the headache of in-house configuration and maintenance. It also gives organizations the ability to scale down as well as up. This agility is something that’s easy to forget because most people associate cloud migration with scaling usage up.
How Can Cloud Solution Be Included in ROI?
Include the following in the calculation of ROI: increased productivity (concentration on core functions), cost reductions, security, network, data storage, and transfer improvements. In a healthcare organization, access is key to improving patient outcomes. It’s important to show how each of these items translates to the ROI. If you can do this effectively, the rest of the C-suite is likely to fall in line with a cloud model.
What Preparation is Needed Before Talking to the C-Suite?
Before speaking to a C-suite individual, the CIO should prepare a model showing the ROI. The presentation should include technical data on cloud-based models that are clearly understood. Documenting a cloud strategy defines the outcomes sought by the CIO, and it’s the beginning of a road map to get there. The CIO’s roadmap should describe how the cloud model will save cost and add efficiencies while improving security and networking reliability. It also has to conform to HIPAA regulations.

by Felicien | Jan 7, 2019 | Education
As businesses add more layers of cybersecurity to their arsenals, cybercriminals are finding new ways to attack system, networks and devices. There is a constant stream of emerging threats that can mean trouble for companies of any size.
Why Is Data Security a Major Challenge Going Forward?
Businesses today are realizing the vast opportunities that come from leveraging, monetizing and collaborating on their collected data. That means companies need to protect their data not only from privacy breaches but also from data misuse, data manipulation and loss of intellectual privacy.
Data validity, for example, is one particular area of cyberattack emerging. Data need not be stolen to hurt the business reputation. Instead, hackers could alter data such that it becomes invalid or inaccurate in such ways to delegitimize business outcomes and partnerships.
Industries need to identify and deploy new technologies that protect data while it’s at rest and in transit. Privacy risks related to data in use are hindering the full realization of data collaboration, limiting the opportunities available to companies.
Here are 8 other cybersecurity challenges that businesses need to combat now or shortly.
1. Chatbots at Risk
Artificially intelligent chatbots have become commonplace, helping to answer questions and guide web visitors to required information and action. Hijacked chatbots, however, could mimic existing tools to drive victims to click on links, download malicious files or share private information.
Web application flaws could also be exploited to insert malicious chatbots into sites that don’t have one.
While these intrusions will likely be text-based bots for now, shortly, speech-enabled bots could lead to further victimization over the phone or other voice-enabled technologies.
2. Artificial Intelligence Mean Powerful Malware
The rise of AI, the Internet of Things and machine learning means more opportunities for business transformation. They also invite more smart attacks using intelligent malware. Cybersecurity providers need to develop new means of detecting these threats and training personnel to recognize and prevent them. Many of these preventative measures need to be automated to provide continuous detection and prevention.
Part of the challenge is the sophisticated tools hackers are using. Updated exploit kits, artificial intelligence and natural-language algorithms have allowed hackers to automate convincing emails. Simple processes allow for the generation of emails to millions of stolen addresses with compelling phishing attempts.
3. Data Exposure
AI-enabled applications rely on data pools to power advanced functionality, both for smaller companies and giants like Amazon and Facebook. The increasing use of data pools means more potential for developers to expose information, often customer data. These data aren’t necessarily subject to hack, but instead are vulnerable and accessible to anyone who can find the vulnerabilities.
4. Cyberwarfare
Bad actors are no longer content on ransomware and phishing attempts. Technology advancements provide new opportunities for targeted and individualized attacks.
These attacks may leverage artificial intelligence to target individuals or corporations. Data integrity attacks, for example, could force organizations to completely replace computer hardware. Physical assaults could use drones and other tools for physical assaults.
5. Infrastructure at Risk
Nation-states will continue to wage cyber attacks on enemies with state-sponsored attacks on infrastructure. Attacks on national security, emergency communications, public health and financial systems could cripple governments and create spiraling consequences for the private sector.
Smaller conflicts could also be used as testing grounds for nation-states to assess new tactics, procedures and technologies that could be used in more significant geopolitical conflicts.
6. Data and Privacy Regulation
In 2018, the launch of GDPR, covering privacy issues for European Union citizens, forced companies to reevaluate their privacy and disclosure procedures. Similar privacy laws were approved in Canada and California. These new regulatory mandates are likely the first wave of protections that will force companies to spend more on cybersecurity, data transparency and reporting. As control of data begins to shift from institutions to individuals, companies are going to need better ways to monitor and report on compliance from multiple jurisdictions.
7. Connected Devices in the Crosshairs
With connected refrigerators, stoves, thermostats, doorbells and washing machines becoming the mainstay in many homes, the possibility of exploits is grave. Hackers will begin to identify and exploit vulnerabilities in these smart devices. Manufacturers will need to build in additional safeguards and architecture to meet growing consumer demand while keeping bad actors away.
8. Industrial Control System Risks
While there are more automated systems to allow for greater control of buildings, utilities and factories, there are inherent risks of exposure. Many of the players providing the technology in this space are new, making high-value targets all the more enticing to hackers.
Each year brings with it new technical innovations sure to drive better business outcomes. At the same time, hackers will find more sophisticated means to create more effective intrusions.

by Felicien | Jan 7, 2019 | Education
In October of 2018, the San Diego Unified School District in California — the state’s second-largest school district — became aware of a severe data breach. As of now, the hackers are unknown, but officials are aware that through criminal means, the hackers were able to obtain the full names, addresses, and Social Security numbers of hundreds of thousands of students and staff at the San Diego Unified School District.
What Caused the Data Breach?
Officials investigating the San Diego school district data breach know that the breach was caused by a phishing scam. They are unaware of exactly when or how the phishing scam occurred, but in some way, hackers were able to obtain access to internal programs and systems in the school district (using a legitimate student or teacher’s login), and from there, they accessed and downloaded the personal information of over 500,000 students and staff members.
What Is a Phishing Attack?
A phishing attack or phishing scam is an illegally engineered attack that aims to obtain personal user data using fooling the target. A hacker will usually find out an account that a target or user group has.
For example, Hacker A might know that their target (an innocent civilian) has an account with Happy Bank in Smithsville. Hacker A will then create an email that looks almost exactly like a real email that would be sent out from Happy Bank. The email will be directed to the name of the target and say something like, “Hi, you need to update your account with Happy Bank. Please login using the following link.”
If the target decides to follow through with the email, they will likely click on the link provided, which will take them to a site that looks almost like the real site of Happy Bank. They will log in using their personal user data (email address or username and password), and probably after that, they will encounter some sort of error message.
By this time, the hackers will already have the user data or personal login information they need from the target. This user data is generally not the endgame for hackers, however.
This user data will merely be used by the hackers to access portals of a larger institution. Although some hackers may use personal login information for a bank, for example, only to steal funds from that person’s bank accounts, other hackers will take things to the next level and attempt to gain broader access and more personal and financial information. Sometimes, these tactics help hackers steal money directly; other times, hackers hold information ransom, extort cash with it, or blackmail individuals or companies by leverage things they know about them.
And remember that the Happy Bank example is just one example of a phishing email scam. Phishing emails and scams can come in many forms, and there are also phishing phone calls that can trip up many people and cause them to divulge personal and financial information willingly.
When Did the Security Breach Happen?
Unfortunately, as of now, the school district does not know exactly when the breach happened. Spokespeople for the school district say that the hack could have occurred anywhere between January 2001 and November 2018 (although the school district did not become fully aware of the breach until October 2018).
This is often the case with phishing attacks. Hackers first need to obtain access to a sensitive information system. To do this, they need login emails and passwords, and phishing emails are the ideal way to achieve this information.
What Information Were the Hackers Able to Obtain?
The San Diego Unified School District is the second largest school district in the state of California and currently serves over 121,000 students.
In this data breach, hackers were able to obtain a large amount of personal information from hundreds of thousands of students in the San Diego Unified School District. Select staff members were affected by the security breach as well, and of those affected, some were even students and staff going back to the 2008-2009 school year. Approximately 50 district employees had their login information taken or compromised.
According to officials, here is some of the additional information that was taken by hackers:
Staff and full student names, Social Security numbers, addresses, email addresses, personal information, and ID numbers
Emergency contact information from students and faculty, including full names, addresses, phone numbers, and email addresses, and employment information
Benefits information for staff members
Compensation and payroll information for staff members, including deduction and tax information, financial institution information (account numbers and routing numbers), and salary and paycheck information
Enrollment information about students, including their schedules, any legal notices, and transfer data on file, records of attendance, and health data
State ID numbers from staff and students
All of the staff members, district employees, and students who were affected by this data breach where notified. Accounts were reset, and cyber-security measures are being taken to prevent any additional breaches of data at the San Diego Unified School District.
How Can You Protect Your Business From Phishing Scams?
Phishing scams are the most notable (and unfortunately, the most effective) modern-day swindle in existence. Whether you own a business, manage or run an organization, or simply want to protect yourself and your family members from hackers, it is essential to learn about phishing emails and how to prevent them.
According to the VP of product management and strategy at Tripwire, Tim Erlin, “The best way to counter this technique … is to have complete and comprehensive logs from all systems.”
It is also vital that everyone in your business knows about phishing emails and how to spot them. Never click on emails or links that look suspicious or slightly “off.” If you are asked to go directly to a website to login via a link in an email, avoid doing so, and instead go directly to the website on your own to log in. Check your messages there for whatever was referenced in the email, or give the institution a call directly to inquire about the email.
Finally, if you own a business or run an organization, always employ the professional services of a high-end IT services provider who specializes in cybersecurity. They will put into place some strong security measures that will help you prevent any sort of security breach, including phishing scam breaches.
by Felicien | Jan 7, 2019 | Education
Downtime, compromised data, security breaches, and slow-running technology cause big headaches for today’s accountants. After all, you need your technology, and when it’s not working, every hour that goes by costs your firm money.
You can’t afford to sit idle—when your technology doesn’t work, neither do you. If your competitors use more efficient IT solutions, they’ll blow right past you and take your clients away. Or worse, your reputation will suffer.
Technology helps you carry out essential tasks, exercise professional judgment, engage with clients, provide advice, and settle tax issues. If you view technology as an opportunity rather than a threat, your firm will prosper and reap the rewards of your efforts. If you don’t, you’ll fall behind the competition.
You use technology now more than ever—at least, you should. Today’s technology is invaluable, and with time it will become even more so. In the past, the accounting profession lagged behind others in the adoption of new technology. They relied on paper-based filing and printed accounting forms that were time-consuming to process.
Accounting firms like yours have now embraced new technology. Just like other businesses, you need to streamline your services to save time and process accounting information. With modern technology like cloud-hosted accounting software, you and your clients can access data directly and simultaneously. The days of shuffling papers back and forth are over.
However, along with technology-provided benefits come some challenges.
Failed backups, slow-running email, application problems, and operating-system crashes create headaches that set up barriers to your success.
Downtime is a threat—it results in a significant loss of productivity. You can’t afford to be faced with server failures, poor systems performance, accidental file deletions, or software application crashes. Without access to your data, you and your employees can’t do your jobs. Money goes out the window, and you can’t meet your filing deadlines.
Data security is another issue that can cause significant headaches. Client confidentiality is your most important duty. But with hackers and intruders who want to infiltrate your technology for their own financial gain, your technology landscape is like a minefield unless it’s adequately protected.
As a Chartered Accountant, you are governed by Rules of Professional Conduct that always have and will continue to guarantee the privacy and confidentiality of your clients’ personal information. If their financial data is stolen, you’ll face penalties, fines, and possibly civil prosecution. You can’t take that chance.
THE ANSWER IS TO CONTRACT WITH THE RIGHT IT SERVICES PROVIDER.
To prevent IT headaches, you need service and support from an IT provider who understands the Line of Business (LOB) applications you use including your financial preparation and planning software and billing systems that keep your operations efficient.
The right provider can ensure these seamlessly incorporate with other applications you use like Microsoft Office or Office 365. When you have access to expertise from an IT Service Provider who truly understands your needs, you can effectively leverage these powerful tools.
Look for an IT Service Provider who has been serving the needs of accounting firms and corporate accounting departments for years. The best choice is one who can cover a broad range of technology requirements through both professional services and Managed IT Services and who can grasp the complexities your accounting firm faces.
They should be able to help you avoid IT headaches when automating routine accounting processes, sharing financial files, deploying mobility solutions, and capitalizing on tools like electronic filing.
Your accounting practice requires a complete technology management solution including data protection and proactive monitoring of all critical functions on your network, servers, and workstations. Plus, you should insist upon a fixed-cost solution with predictable budgeting. Just as your accountants are committed to your clients’ success, your IT Service Provider must be dedicated to making you successful and view themselves as an extension of your practice.
Your IT Service Provider should be adept with:
Cloud Technologies that improve your productivity, efficiency, and security
With cloud solutions, you can eliminate the cost of paper and the hassle of sifting through files, store massive amounts of information (Big Data), share important files in real time and secure your clients’ information offsite in high-security data centres.
Accounting Practice Management Software that helps you run day-to-day operations including the centralization of client data, tracking due dates, staffing, workflow management, automated billing, and time tracking
Tax Preparation and Filing Software designed explicitly for accounting firms, so you can analyze different income tax scenarios and have access to the reporting tools you need for fast, easy reconciliation
THE WORST HEADACHES RESULT FROM IT SECURITY BREACHES.
Data breaches are increasing exponentially. Cyber mafias have set up in towns like yours, operating from legitimate-looking offices. Hackers are no longer kids in their parents’ basements working on a few computers. Cybercrime is an international and sophisticated business with cartels operating around the globe.
Your data is valuable, and your accounting firm is a target. You need the expertise of an IT Service Provider who stays up to date on the latest threats. It’s imperative that you protect client information. But IT security best practices change so rapidly that accounting firms often find themselves falling behind the curve. If you do, your firm is at risk of viruses, network vulnerabilities, and data breaches. This results in more than a headache; now, you’re looking at a migraine.
Criminals have many ways of stealing your data.
Internet Exploits
Your employees use connected devices to interact with, track, monitor, and simplify just about every area of their work and personal lives. However, these technologies also provide access to sensitive, confidential information and present a wide variety of new security issues for attackers to exploit.
Third-Party Attacks
Cybercriminals have learned that contractors and other third-party providers aren’t as secure as large vendors, and lower security provides a pathway into otherwise-secure networks. Examine who can connect to your network and access confidential information, even if you believe appropriate security measures are in place.
Social Media Attacks
Social media presents two main security headaches:
A website you visit or service you use can be infected with malware that spreads until your network is ripe for a data breach. Malicious social media content is expected to grow 400 percent as attackers continue to distribute their malware and steal client data.
A determined hacker or team can scrape social media sites to assemble a surprising amount of personal data very quickly. This data can be used to engineer an attack.
Social Engineering Attacks
Human nature is easily the weakest link in any security chain. Was that really a utility-company employee you held the door for this morning? Are your office painters propping open a secure entrance to make their task more manageable? Did your receptionist just give all your passwords and hers to someone who called claiming to be from tech support on another floor? Will your colleague’s curiosity causes him or her to insert the USB key “found” in the parking lot into a computer connected to your systems?
Mobile Malware Threats
Security experts have been warning us about mobile malware threats for a long time, and users have grown immune to these warnings. Mobile-device use is increasing, as is the sophistication of attacks. At the risk of being the boy who cried, “Wolf,” every year a major mobile malware attack is more likely to occur. Attackers typically select the most significant number of potential victims. So, they will target mobile devices, specifically Android and jailbroken iOS devices.
Sophisticated DDoS Attacks
Distributed Denial-of-Service attacks don’t directly steal your information. Instead, they overwhelm your site or service with so much traffic that it prevents legitimate users from connecting. These attacks have evolved beyond simple flooding of traffic. They probe and then morph, based on the defences in place on your network. Such advanced and sophisticated attacks can seriously impair your accounting firm’s operations.
TO PREVENT THESE SECURITY HEADACHES, YOU NEED A SECURITY PLATFORM WITH REMOTE-ACCESS MONITORING AND RELIABLE BACKUP AND DISASTER-RECOVERY SOLUTIONS.
Be sure your IT Service Provider implements innovative, up-to-date security measures to protect your accounting firm against intruders, malware threats, and disasters. And ensure they can do the following things
Ensure:
You comply with accounting and confidentiality requirements when using technology.
You use appropriate technical means to minimize the risks of disclosure, discovery, or interception of communications.
Data and email are encrypted to protect your sensitive information.
You adopt management practices that offer protection against disclosure or discovery of electronically transmitted messages.
Prevent:
Unauthorized access to your electronic data
Computer viruses from damaging your data
Natural or manmade disasters from affecting your IT operations
Confirm:
Your files are reliably backed up and recoverable.
Both offsite and onsite data backups are maintained.
Data is restorable by performing ongoing testing.
Provide:
Systems Analysis
Mobile Device Management
Up-to-Date Security Solutions
User Support and Training
Your IT Service Provider should implement a security platform with multiple layers of protection, with 24/7 remote monitoring to detect infections and intrusions, and block them before they get in and steal or hold your data hostage. Many accounting firms are unaware that this goes on. Your IT provider will keep you informed and train your staff to recognize threats, so you know what to do if one comes across your computer screen.
Your very most basic security solution should include barriers with virus and malware detection at the firewall level and DNS (Domain Name Server) controls to ensure your users don’t visit hijacked websites. Your employees should also utilize two-factor authentication access practices to prevent criminals from getting into your network.
Nothing is more important than protecting the information on your network and the peace of mind that comes from knowing you can fully recover if a disaster hits your firm. Your IT provider must ensure your business continuity and disaster recovery solutions will meet your objectives and must implement a robust backup and secure off-site replication solution.
While computer systems can easily be replaced, the intellectual property and sensitive information stored on those systems cannot. Computer hard drives can fail, laptops can be stolen or lost, and data can be erased due to human error or viruses. It’s important for your accounting firm to have a backup system to keep data safe and avoid data loss.
Ask your IT Service Provider if they employ system virtualization and a private cloud with a fully redundant system that can be replicated across multiple data centres. If your data is compromised or damaged, a new clone of your system and data can be spun up with a new, fresh image in a manner of seconds.
Be sure your IT provider uses an Intrusion Detection System. This will catch anything that may have bypassed your firewall. They can either be used to find a break-in attempt in progress or detect one after the fact. In the latter case, it’s too late to prevent any damage, but at least you’ll be aware of the problem.
If an intruder gets into your system, the first thing they typically do is install a “rootkit.” A rootkit is a script or set of scripts that can make changes to your IT system and hide in common system utilities. They function in the background without your knowing they are there. Criminals can easily obtain these on the Internet. This is one reason you must have reliable backups of your entire IT system. If rootkits are discovered, you’ll need to re-install your system and data and start over from scratch.
Your mobile devices also require monitoring and management. If a phone or laptop is stolen, you must be able to remotely wipe your confidential data. Mobile Device Management also prevents disgruntled employees from leaving with your confidential or proprietary data.
Your IT Service Provider should also employ encryption to protect your confidential data. They should encrypt both your emails and data files to ensure the security of information. Encryption can protect your data at rest, such as on laptops or portable servers, as well as data in motion, such as over wireless networks or the Internet.
One of the most overlooked security aspects in accounting firms is their creating and retaining policies regarding email and data. You are accountable for instituting and employing a strategy that details the duration over which your client data and emails will be stored and deleted. Ensure your IT provider can implement automated solutions to handle this.
IN CONCLUSION
You understand the unique challenges and technology demands your accounting firm faces. Whether your IT headaches come from the security risks of handling and storing confidential information or the difficulties of keeping up with new, innovative Line of Business Solutions, you need an IT Service Provider who can ease your struggles and your IT headaches.
by Felicien | Jan 6, 2019 | Education
If there’s a will there’s a way when it comes to scammers, especially with gift cards. Everyone loves gift cards. Consumers love how easy it is to purchase gift cards, use gift cards and even give gift cards. It’s as simple as buying a card at a brick and mortar store or clicking a few buttons and almost instantly having the funds needed to play. Scammers love gift cards too. Gift cards can immediately be activated and spent by these scammers even before the owner of the card knows what happened.
Google Play gift cards are targets right now. Scammers love how easy they are to steal so consumers need to stay one step ahead of these online crooks. Here’s one of the latest Google Play Gift Card Scam that is scouring the internet.
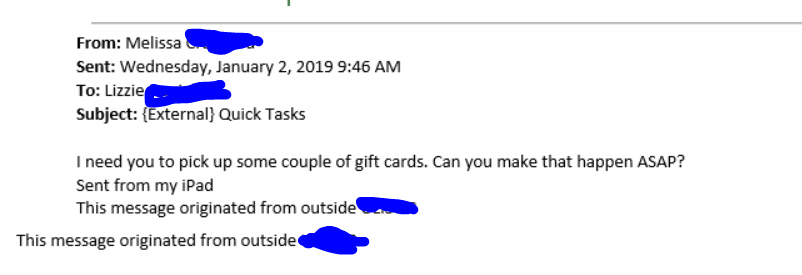
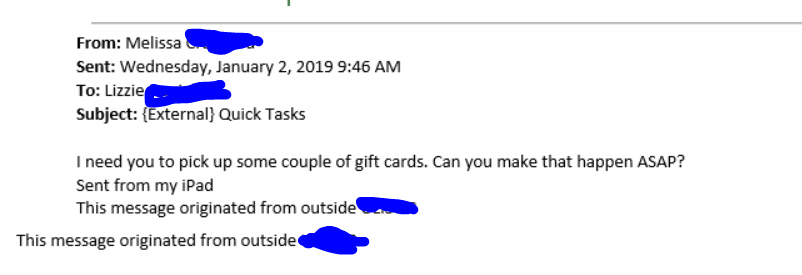
Scam Alert: Currently there is an email scam occurring where thieves, posing as someone the recipient knows and are phishing for personal, financial, and other private information. This includes requests for Google Play Gift Cards. For example, the message will read, “I need you to pick up a couple of gift cards. Can you make this happen? The type of gift card I need is Google Play gift cards. I need 4 cards in $500 denominations…scratch the back of the card to reveal the card codes and email me the gift card codes.”
Take away: Never provide any personal information including gift card codes like Google Play in an email. What seems like the information is going to a trusted source, it could be a scam.
by Felicien | Jan 4, 2019 | Education
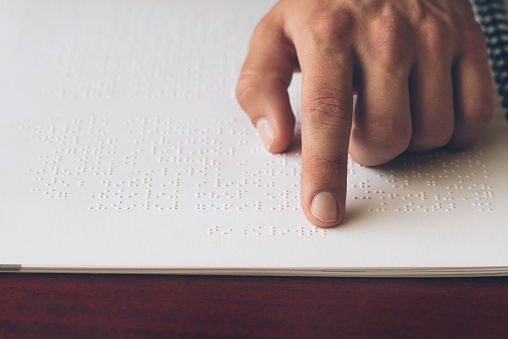
On January 4th, 1809, Louis Braille was born. Louis Braille was a child who lost his vision in an incident involving a sharp tool at the age of 3. During his early life, Louis had an interest in “night writing”, a military code used by the French Army in the 1800s. This “night writing” was a way for soldiers to silently communicate in the dark. At 15 years old, Louis Braille simplified the French soldiers’ code so that it was easier to use and understand. This was the beginning of the Braille System that is still used today.
Braille is a system of raised dots that are felt with fingertips to give blind people a way to read the words around them. The raised dots are arranged in a way that represents letters, numbers, and other characters. There are two different versions of Braille. The first is uncontracted, where each word is spelled out. The second is contracted, similar to shorthand. There is also a type of Braille, the Nemeth Code, that is for working with mathematics.
World Braille day reminds us of the impact that Braille has on the daily lives of people living with blindness. Braille is a key factor in obtaining literacy equality. Without braille, people with blindness or vision loss wouldn’t be able to read anything on their own. Braille helps people to live more independently.
On World Braille Day, further, educate yourself on braille. Learn about all the ways that it makes life easier for those who are blind. You could even join groups that help incorporate Braille into more parts of everyday life.