by Felicien | Dec 26, 2018 | Education
Data breaches and phishing scams are becoming more popular among cybercriminals. There have been so many data breaches, in fact, that the chances that some of your private information has been discovered by online scammers and sold to other ones are pretty high. One of the most significant data breaches in recent years (that has been discovered….many large ones haven’t been discovered yet) was at Anthem Blue Cross/Blue Shield. If you are concerned you may have been a victim of that particular data breach, there are some things you should know, as well as things you can do to minimize the damage to your credit and identity you may have experienced.
Anyone who has been a customer of Anthem Blue Cross/Blue Shield in the past decade is a potential victim of this data breach, and should thus take some steps to do damage control, whether they have noticed anything odd in their credit report or use of personal information. Potential victims also include those who used the Blue Card in any area affiliated with Anthem during that period.
It is not only a data breach at Anthem that should be of concern to current and past customers. Anthem has also issued a warning about a phishing scam mimicking calls and emails from their company. The scammers will ask for personal information when they contact you, such as Social Security numbers and credit card numbers, which are all things Anthem never asks for in these ways. They will never ask for this information as a means to identify you.
Anthem has been working closely with a well-known and well-respected security firm called Mandiant to mitigate the damage from the data breach and phishing scam. It has also been working in close conjunction with the FBI to discover more about the origins of the data breach, which was discovered in January of 2015.
In the data breach, the following things were stolen from Anthem’s customers:
Names
Dates of birth
Social Security numbers
Home addresses
Personal email addresses
Employment information
Income
Anthem health ID numbers
Anthem is offering current and former customers who may have been impacted by the data breach two years of free credit monitoring and credit repair services if needed. Most of the customers who have or may have been affected by the data breach were sent letters in February. The letters let customers know about the breach, how it may impact them, and that it took place across several weeks in December of 2014. The letter also warns current and former customers of the phishing scam that is ongoing.
Anthem is particularly calling out to customers in the letter to let them know that they are not phoning or emailing them about the data breach, and are not asking for any credit card numbers or Social Security numbers over the phone.
In fact, the phishing scam appears to be attached to the data breach, either being done by the people responsible for the data breach, or by people taking advantage of it. The scammers behind the phishing scheme know about the data breach and are using people’s concerns about their personal information being involved in it to get them to give their most sensitive information in a belief that Anthem will use that information to protect them against being affected by the data breach.
While some people are receiving phone calls in the phishing scam, with the telephone numbers looking like they are coming from Anthem, others are receiving emails. The emails include a link that says “click here” to sign up for free credit monitoring. Anthem is already automatically giving everyone affected or possibly affected by the breach free credit monitoring, so the emails are not coming from Anthem, even though they are made to look like they are. Anthem is quite clear in its letters to customers about the breach that the emails are not from them.
Those who are concerned they may have been affected by the Anthem data breach are being protected by Anthem, but there are additional steps they can take. These additional steps ensure the maximum level of protection now and in the future. Some things that people can do to protect themselves include:
Changing their passwords on just about anything they do online, but particularly email, financial accounts, and social media.
Get a copy of their credit report from all three credit bureaus and place a fraud alert on them.
Dispute any items on their credit reports that are not real.
Closely monitor transactions on any credit, debit, or bank accounts, and reporting any suspicious or fraudulent activity to the bank or credit card companies involved.
Doing these things will give individuals a sense of control over their potential exposure in the data breach, and will also go a long way toward helping ensure their personal information and finances stay protected.

by Felicien | Dec 26, 2018 | Education
Chief information security officers face new and stronger threats to systems in 2019. Not only are hackers deploying more sophisticated attacks, but attackers have new targets in their sights. Also, geopolitics and consumers will continue to play an outsized role in discussions of cybersecurity issues.
Knowing what horizon issues will help CISOs to plan accordingly and deploy solutions that are ahead of the looming problems.
What New Technologies Are Hackers Using?
One growing threat is botnets, in which hackers compromise hundreds, thousands or millions of infected computers. Hackers run command-and-control networks to manage these zombie computers.
One widespread use of botnets is distributed denial of service (DDoS) attacks, which flood domains with so many requests that they can’t handle real inquiries. Often websites crash and are not recoverable unless a ransom is paid.
Botnets are delivered via worms, which attack spreadsheets and documents, and viruses that target systems, destroy data or make networks inoperable. Once implanted in a system, viruses and worms spread, infecting more computers and doing more damage to files.
The challenge for CISOs is to remain ever-vigilant in this front line of attack. Anti-malware software that is continuously running in the background and automatically updated is one key solution. However, companies large and small also need to stay on top of the software, hardware and operating system upgrades, making sure that all devices and programs are updated. These protections need to be in place both for core system servers and end-user devices.
Finally, an in-depth defense should involve regular, meaningful and compelling personnel training that makes employees aware of how to avoid phishing traps and remain suspicious of unknown or unfamiliar emails and attachments.
Are There Other Risks from Hackers?
Hackers frequently use the Dark Web to trade, share and buy information. As defenses get more complicated, hackers become more determined to find new ways to thwart preventative measures.
Take, for example, exploit kits, which are traded regularly on the Dark Web. Hackers do not issue attacks in one fell swoop. Instead, they sniff and explore different aspects of a target. While malware and phishing schemes target end users, other tools are deployed to explore the system’s website and perimeter.
Exploit kits are self-contained, all-in-one tools that are developed with discretion in mind. If a hacker finds a vulnerability on a website, it can attack the server that hosts said site. When a victim visits the website, they are redirected to a rogue server instead, which gathers information about the victim. The exploit kit identifies and delivers an exploit that is attached to the victim and downloaded onto the victim’s computer, often via a software security hole.
Another example is an APT (advanced persistent threat). Another stealthy hacker tool, the APT can enter a system network and lie dormant until activated. APTs don’t do file damage but steal financial and other critical information. When login credentials are taken, the APT can dive deeper into a system to compromise even more data.
Then there’s the drive-by download attack. Such attacks don’t require any action on the part of a user. Malicious code is downloaded automatically upon visiting a URL via a browser, operating system or app. Often these attacks contain multiple pieces of code that infiltrate the system in the hopes that a few get past your defenses.
Stopping these attacks means updating browsers, using anti-malware tools and deploying sophisticated firewalls that monitor and protect the network’s perimeter. Intrusion detection systems and alerts can identify, contain and neutralize many of these threats before they cause significant damage.
What About Blockchain and Cryptocurrency Defense?
The growing application of blockchain technology in many areas has led to new opportunities for theft of these assets. While blockchain can be difficult to hack, mining for cryptocurrency is a lucrative endeavor.
The challenge with mining for crypto is it takes a tremendous amount of computing power. Hackers are hijacking (cryptojacking) corporate and personal computers to take advantage of their processors to mine. It’s a passive way for hackers to make money, but can dramatically slow down computer performance and add to utility costs. As long as cryptojacking remains profitable, it will be a headache for CISOs.
Do I Need to Worry about Cloud Data?
More companies have shifted data and applications to the cloud, breathing a collective sigh of relief that the protection and monitoring of that information are in the capable hands of a trusted third party. However, companies often deploy cloud data solutions without investing in the underlying security, particularly encryption. That means many companies have unsecured information stored in the cloud that is easily accessible to anyone who might want to use, steal, manipulate or alter it.
Hackers are shifting their tactics about how to disrupt data. Instead of stealing it, they are manipulating data. Data manipulation attacks can do serious harm to company reputations as data users question the reliability and accuracy of data sources. The impact on information providers, financial institutions and medical practices and hospitals could be devastating if data are altered such that an organization’s integrity is questioned.
What About Data Regulations?
In 2018, two significant regulations came into being. The General Data Protection Regulation (GDPR) governs data protection and privacy for citizens of the European Union and affects any organization that does business with said residents. California passed a sweeping online privacy law that affects consumers and requires companies to disclose on demand specific uses and sales of consumer information.
More regulation is likely. With more regulatory complexity will come additional challenges for CISOs.
Consider that Europe, China and the U.S. have very different approaches to data and its regulation. China takes a very nationalistic view of data, seeing it as something to be protected and contained within the country’s borders. Europe considers data as something that needs to be highly protected and kept secure.
The U.S. has seen data as a commodity to be commercialized, sold and leveraged for financial gain. There is very little unifying federal guidance on data security like Europe’s GDPR.
In the U.S., companies could face different data privacy requirements from each state if others take California’s lead.
What does this mean for companies? A complicated regulatory landscape. There will be difficulty in gathering, storing and using data from multiple jurisdictions. It could also lead to greater compliance issues as companies need to grapple with similar but distinct reporting standards for different states, countries or regions.
What Political Concerns Affect Cybersecurity?
The U.S. is embroiled in several controversies with other nation-states related to cybersecurity. Ongoing investigations about Russian intervention in elections, trade wars with China, and concerns about trade agreements in North America and Europe add to a climate of political uncertainty. Cybersecurity will likely continue to be a political issue both domestically and internationally throughout 2019, especially in the lead up to the 2020 presidential elections.
How Are Consumers Affected?
As consumers and companies become more interconnected, hackers are shifting their targets away from corporations to consumer devices. This concern becomes more significant with the vast proliferation of the internet of things. With smarter, connected devices in use comes added vulnerability. Hackers could, for example, attack a smart television and hold it for ransom. Connected toys could become a target for child predators. Already there is an increase in sextortion attacks designed to shame victims into believing their visits to porn sites were recorded and will be released if a ransom isn’t paid.
While these consumer-based issues may not directly affect CISOs, they will if the attacks come from your devices or services or a result of data stolen from your company.
What Issues Arise from Passwords?
In recent years, multi-factor authentication has grown. Simple passwords continue to be a prime target of hackers. Password theft and password-related breaches become less prevalent and relevant for companies that deploy low-cost multi-factor solutions.
How Can We Combat Shadow Systems?
Ego, internal politics and budget often make it challenging to address rogue and shadow IT systems. The reality is that shadow IT systems not governed, maintained or monitored by central IT staff are a significant liability. With increased awareness and understanding of cyber threats, CISOs should use 2019 as a time to finally pull the plug on rogue systems.
Each year brings new complexities and challenges to IT security officers. Getting ahead of these issues and making sure your organization is ready to address them is a valuable new year’s resolution.
by Felicien | Dec 24, 2018 | Education
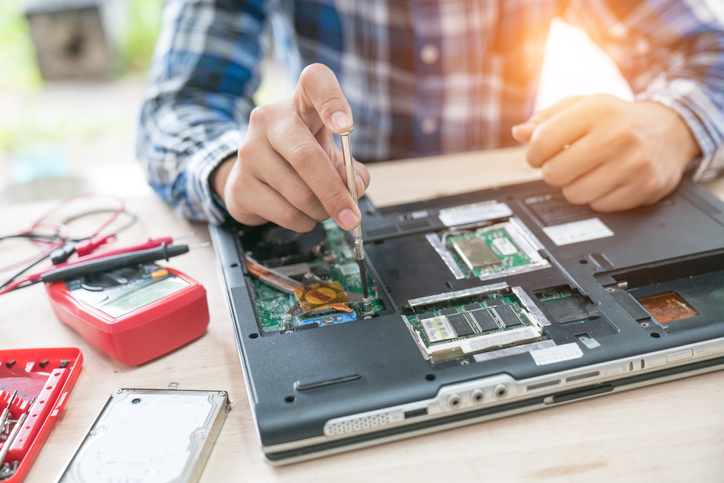
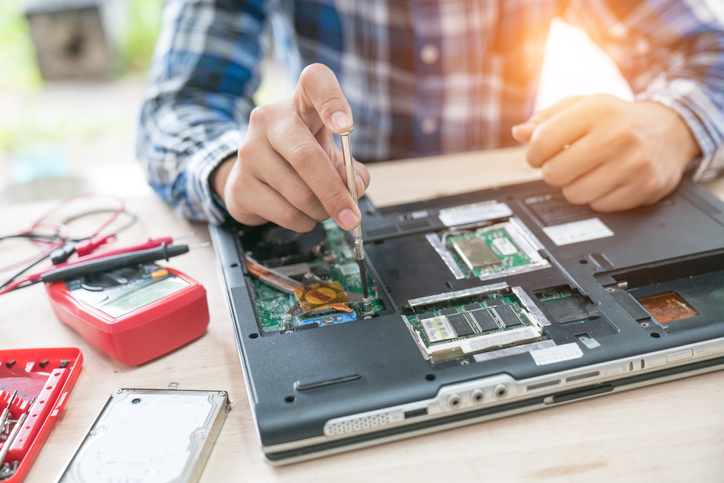
Computer systems have a way of breaking at the worst possible time: in the middle of your business’s rush season, right before a long weekend or when your regular IT technicians are on vacation. When this happens, many organizations call a repair service, looking for an estimate on getting back to work as quickly as possible. While this can be an acceptable solution in the short-term, it can become quite expensive regarding lost productivity and direct costs over a more extended period. When you’re not able to plan ahead for the costs associated with a problem, you may find that your IT budgets are short when you get ready to implement the “next big thing” for your business users. Reduce the overall risk to your business and protect your ongoing profitability by implementing a managed IT services model.
What Are Break/Fix IT Services?
At their most basic, break/fit IT services are precisely that — when something breaks, you call someone to fix the problem. While this is a highly simplistic explanation, it represents a more reactive approach to technical problem resolution. Instead of actively looking for ways to partner with organizations to enhance their security, shore up problems and enhance usability, companies who specialize in break/fix solutions are waiting to hear about a problem before they jump into action. When that happens, technicians work with your business remotely or come onsite to diagnose the problem, ultimately charging your business an expansive hourly rate for the resolution. You pay only for services that you’re using when you need to use them. While there are no monthly or ongoing fees, it can be complicated to predict when you’re going to have a problem or the extent of the costs required to fix the issues.
If the technician you work with doesn’t have experience with your particular platforms, they may spend a fair bit of time getting up to speed and researching the issue and resolution. If the problem isn’t fixed the first time, you’ll be charged each time technicians spend time working with your business. It’s difficult if not impossible to predict long-term support costs with this model and since technicians are paid by the hour, there isn’t a compelling case for them to quickly come to a resolution that gets your teams back online.
How Are IT Managed Services Different from Break/Fix?
With an IT managed services model, you’re paying a consistent monthly rate to ensure that your business infrastructure remains secure, scalable and accessible. An IT managed services contract often includes guaranteed uptime and specific expectations around how quickly questions or answered or solutions provided. This means that your IT department is able to accurately project costs over time while still maintaining a high-performance, complex environment. This type of model allows your technology team to offload many of the day-to-day tasks associated with infrastructure management, such as:
Password resets
File and folder recovery
Application of software and security patches
Virus and malware protection
Server scaling
Software license management
Business continuity and disaster recovery solutions
Mobile device management
Security and compliance support
Each of these services provides a unique value to your business while allowing IT professionals with the capacity to push internal business and technology initiatives forward.
Enhanced Security Solutions
A key concern for businesses today is the security of systems and data — both information that is in transit as well as at rest. With a managed services IT provider, you have the assurance of a team of security experts actively reviewing your business’s security and performance metrics. Proactive monitoring of a wide range of systems from a central interface allows your managed services partner to offer proactive recommendations to enhance your security as well as spot problems and begin immediate remediation. A data breach can cost your business thousands if not tens of thousands of dollars, but a quick catch of a vulnerability can often be patched before cybercriminals have an opportunity to slip through your security procedures. This augmented security posture is particularly important for organizations storing personal, health or financial information for their customers.
Whether you are currently looking for an IT services partner or just exploring the idea of moving in this direction, the benefits are clear. More predictable cost structures over time, a deeper well of expertise on which to draw and the ability to quickly return to productivity are all compelling arguments for this proactive approach to your information technology infrastructure.

by Felicien | Dec 23, 2018 | Education
Most of the time, a five-day vacation is something to look forward to, but if that vacation is unplanned and filled with anxiety over when you can get back to work, it’s probably not much of a holiday. It becomes a burden; financially, emotionally and even physically on everyone involved.
This is what it feels like when ransomware attacks a practice. Get ready to cancel all of your appointments, damage patient trust and pay HIPAA fines on top of it all.
And no, ransomware isn’t exclusive to big hospital systems. Small to medium medical and dental practices are prime victims because the hackers know that many such practices are more vulnerable to these attacks.
Here’s what you need to know.
What Is Ransomware?
Ransomware is a particular type of malware that encrypts all of your patient files so that you can’t access them. The hacker then demands a ransom in exchange for unlocking the data. In some cases, the hackers keep up their side of the deal. In other cases, they take the money and then sell your patients’ information on the black market, turning this into a compliance and regulatory nightmare. As more medical practices have worked to increase security over the past several years to comply with compliance standards like HIPAA in the US or PIPEDA in Canada, dental practices become even more of a target.
According to Sylvia Burwell, secretary, U.S. Department of Health and Human Services, “Cybersecurity is one of the most important challenges we face as a nation…Unlike many cyber threats, ransomware is immediately disruptive to day-to-day business functions and, therefore, your ability to provide high-quality health care.”
According to the Office of Civil Rights (OCR), which is the federal department that enforces HIPAA compliance, around 4000 attacks happen each day. Having proven lucrative for the thieves, these attacks are on the rise.
How Does Ransomware Happen?
Hackers have many virtual windows they can climb in through to access your files. Some common methods used are very inconspicuous yet effective like:
Sneaking malware to a 3rd party software
Attaching the malware to a link in an email that appears to come from a known, trusted source (a dental insurance company, coworker, etc.)
Placing a file on a website that automatically downloads when someone visits the site
In some cases, hackers find clever ways to gain access to computers that aren’t even on the Internet.
How Do You Prevent Ransomware in a Dental Practice?
The American Dental Association (ADA) reminds dental practices that the OCR has established several steps you can take to protect yourself from these attacks, including:
Implementing in-office protocols to reduce risk
Educate yourself and employees about how malware might enter your computer system
Limit who has access to PHI
Have a separate backup for patient files that can be accessed in an emergency
Also,
Install a firewall
Do not allow employees to access public wi-fi with devices that may communicate even through email with office computers
Keep all software and virus protection up-to-date to stay protected against emerging risks. Hackers are continually updating their malware to bypass existing security and exploit newly discovered vulnerabilities. When companies find these, they immediately push out a patch to their customers. But customers must install them promptly to become protected.
Be mindful about 3rd party software. Culturally, we’re so accustomed to thinking that “there’s an app for that”, that we put little thought into how safe the convenient 3rd party programs are
If you suspect that one of your computers has been infected, take it off the network immediately to reduce the risk of the infection spreading.
Only allow a knowledgeable IT professional to work with the infected computer
Work with your IT team to institute safety measures and track employee compliance with those measures.
Does Ransomware Impact Dentists Too? Absolutely.
Any business who would be negatively impacted by having their customer data encrypted is a possible target. As larger practices increase security, smaller entities like dental professionals find themselves a more enticing target. You can take steps to significantly reduce your risk. For more information on keeping your practice safe, follow our blog.

by Felicien | Dec 21, 2018 | Education
When computers or network systems break, you need to know that you’re able to quickly get your teams back online and to full productivity. That can be a challenge, especially if you’re working with a computer repair company. You can’t predict when a problem is going to occur or guarantee that a technician who is comfortable with your network configuration is able to quickly resolve the problem. This can be a costly issue for your business, not only in terms of the direct costs of hiring a computer repair tech, but also the indirect costs of lost productivity and customer frustration. When you work with a computer support company, you have the peace of mind knowing that there are set parameters around their response times and ability to solve specific problems. With a structured ongoing cost structure and myriad business benefits, many organizations are choosing to outsource to computer support companies.
What Are the Benefits of Using a Computer Repair Shop?
If you use the same computer repair shop for a long period of time, you may develop a relationship that allows you to quickly describe the problem and receive the resolution. However, you may find that you need multiple repair partners in order to successfully support all of the software and hardware that make up your IT infrastructure. You will only pay for the items that break and need to be fixed, so there are no monthly or quarterly costs that need to be budgeted. This approach also allows your technology team to assign tasks to internal staff members for resolution if they have time available. While these are strong benefits, there are some negatives to this approach as well.
Why Should I Use a Computer Support Company?
Using a computer support company, also known as a managed services provider, helps fill in some of the gaps that are left with a simple break/fix repair shop. While computer repair shops are often able to resolve a specific problem, they are unlikely to provide your business with the proactive security and technology management that will help you remain competitive in the future. The ongoing costs of working with a computer support company also ensure that you receive a high quality of service — guaranteed. You’re able to offload some of the more time-intensive daily tasks that can be a drain on internal IT time such as resetting passwords or restoring files. This allows internal IT staff to become a more active part of the organization’s digital strategy by contributing thought leadership and active engagement with business users to move the organization forward. An IT managed services provider is always on the job: reviewing your security posture, applying bug fixes and security patches to software, actively managing software licenses and ensuring that your network infrastructure remains stable.
Security Benefits with IT Managed Services
Applying hotfixes and patches is one of those ongoing tasks that can be difficult to prioritize on a daily, weekly or even monthly basis — but they are crucial to the ongoing security of your network and computers. Since IT managed services providers are paid whether or not you have a major outage, they are incentivized to create a high-availability environment that includes fewer slowdowns and limits the possibility of a breach. Any network security concerns are addressed immediately, by a team of professionals who are well-versed in various software platforms and security procedures. You’re also able to leverage best practices from across a range of industries to ensure that any sensitive personal, financial or health data is well-protected by the best possible security procedures.
Making a decision between a computer repair shop and a computer support company ultimately rests on the importance of stability to your business. While an IT managed services model may seem more expensive due to the ongoing monthly cost, it’s important to factor in the expense associated with a major breach and productivity losses due to downtime when you’re making a decision.